The SINET 16—Start-ups to Watch
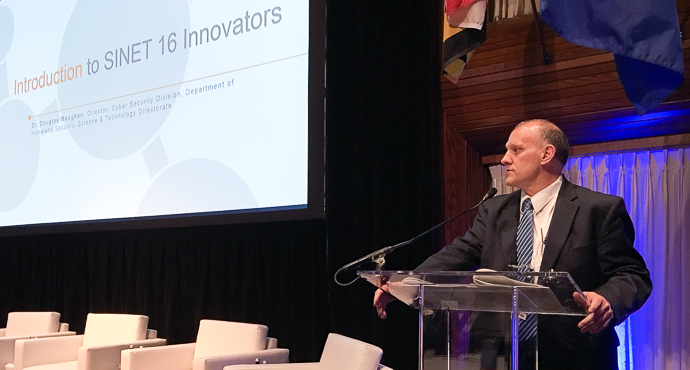
Doug Maughan, of the Department of Homeland Security Science and Technology Directorate, welcomed and introduced the companies honored as this year's SINET 16 innovators. The Directorate has long been a partner and supporter of SINET, and Maughan expressed gratification at being able to introduce the latest class of the SINET 16.
This program involves evaluation of hundreds of emerging cyber security companies from around the world. This year's winners included companies not only from the US, but from Canada, Israel, and the United Kingdom. The judges take into account the companies' technology, products, and business models. The sixteen companies selected present themselves and their offerings at the annual SINET Showcase.
This year's class was marked by its exploitation of big data, anomaly detection, behavioral analysis, and machine learning. And all of 2016's SINET 16 were vividly aware that the users of their products operate against an intelligent adversary who thinks, reacts, adapts, and creates. Here are this year's SINET 16, as they described themselves.
Blackridge Technology: caller ID for the network.
Blackridge Technology was introduced by its CEO, Bob Graham, who characterized Blackridge's offering as "caller ID for the network." Blackridge cloaks networks and protects them from "problematic users." The company's product authenticates before establishing connections. Offering first-packet authentication, Blackridge's technology integrates with existing infrastructure and can be deployed through a variety of flexible deployment options. It also affords protection against a range of insider threats. Originally a product developed for the Department of Defense, Blackridge now has commercial OEM customers (including IBM), and expects to be qualified soon by a major bank.
Contrast Security: self-protecting apps.
Contrast Security's CTO Jeff Williams described his company, which describes itself as a vaccine for applications. Complexity, he said, effectively precludes scanability, this raises the question of whether software could protect itself. Making apps self-protecting is Contrast's approach. The company delivers security in a single application layer solution. This is a distributed solution—"your apps protect themselves across your enterprise." Williams said that Contrast offered the accuracy and speed necessary to reduce an enterprise's reliance on expensive human labor.
CyberX: securing the industrial IoT.
Omer Schneider, CEO of CyberX, described his company's role in securing the industrial Internet-of-things. With operations centered in the US and Israel, CyberX addresses the challenge of securing the industrial IoT, where highly motivated attackers go after soft, easily hit industrial targets. He characterized the company's flagship product, XSense, as one that continuously monitors an industrial network, collecting data in real-time to detect unfamiliar activity that potentially threatens that network. It features machine learning, modeling, and state machine design.
DataVisor: forecasting attacks with unsupervised analytics.
DataVisor offers innovative fraud detection. Its vice president of marketing, Mike Flouton, described their offerings. He began by pointing out that fraudsters are as agile and adaptive as hackers, but the typical defense against fraud is reactive, and requires prior knowledge of the likely attempts. DataVisor uses unsupervised analytics, which are preventive by nature. Its big data analytics can shift the line of first detection from attack to incubation—it catches nine out of ten fraud attempts during incubation and before exploitation. The solution's big differentiator is its ability to scale without imposing a prohibitive computational burden on the enterprise it protects.
Digital Shadows: delivering needle-rich haystacks.
James Chappell, CTO of Digital Shadows, described his company's offering. Every organization casts digital shadows they're unaware of. Such shadows include data leakage and other routine exposure to the Internet. These shadows, combined with the attacker's view, and the attacker's footprints, combine to make up cyber situational awareness. But the sheer volume of information to often and too easily defeats efforts to achieve and maintain situational awareness. Digital Shadows' platform offers collection, collation, analysis, and dissemination. Instead of forcing an enterprise to hunt for the proverbial needle in a haystack, Digital Shadows delivers "needle-rich haystacks."
Interset: threats inside the network aren't just insider threats.
Dan Quayle, Interset's CEO, drew a distinction between threats inside the network and insider threats. Threats disclose themselves through anomalous behavior. The challenge lies in distinguishing real from merely apparent threats. A realtime discernment of risk enables swift action. Interset provides automated behavioral analytics that can deliver over-taxed analysts a perspicuous representation of the data they need to recognize and respond to threats operating inside their network. Interset uses big data techniques to drive data to the top of the team, and then it automates an appropriate response.
Menlo Security: security through isolation.
Menlo Security's co-founder and chief architect Gautam Altekar described his company's approach to eliminating the threat of malware. They don't, like legacy systems, focus on detection. Instead, Menlo Security's approach is isolation of all content. They focus on a web use case—an isolated browser that keeps content off the endpoint, but provides the bidirectional communications users need. Their key technology is adaptive, clientless rendering, with a transparent user experience. In production since early 2015, Menlo Security's solution can isolate email links, provide Flash isolation (delivering content without risk) and all-web isolation.
Passages: user-resistant security is user-friendly security.
Passages' Chief Scientist, Lance Cottrell compared malware to vampires: they can enter only when invited. Passages (and Passages is an Ntrepid company) offers a virtualized browser that prevents exactly this kind of invitation. It also addresses the risk of targeted attacks, and scans downloaded files. Users of passages always start with a clean browser, which provides "user-resistant security" of the kind necessary to making effective use of the Internet—user-resistant security is user-friendly security. Passages also offers anonymous browsing. A clean browser and anonymity give users "All the web without the risk."
Phantom: who executes faster, wins.
CEO Oliver Friedrichs described Phantom. He began by asking all to consider the OODA loop—observe, orient, decide, and act. Who can execute that loop faster, wins. Phantom automates decision-making. They offer an open and extensible platform that lends itself to integration with point solutions. Use cases show how Phantom can automate defenses in ways that reduce thirty minutes of checks to thirty seconds. Engineers love Phantom's solution, Friedrichs said, because it's Python-bases. And, for those customers who don't know or aren't comfortable with Python, Phantom also offers an easy-to-use, high-level interface.
Post-Quantum: science fiction reduced to engineering.
Post-Quantum's CEO Andersen Chang began by asserting that "quantum computing is now engineering, not science fiction." The challenge in sharing data lies in determining whether a sender is true, right, and has authority. Post-Quantum offers a split key cryptographically, then redistributes and reconstructs enough of it when needed. Their modular cyber security toolkit includes Authentication and Non-repudiation, Secure Communications, and Quorum Approval. And, since it's reduced science fiction to engineering, Post-Quantum has significant customers who rely upon it for incident prevention. Those customers include Her Majesty's Government, NATO, and major banks like Barclays.
Prelert: see the real anomalies, not just the apparent ones.
Prelert, now an Elastic company, helps display anomalies and enables analysts to understand those anomalies' significance. Elastic's Dave Erikson introduced Prelert's solution by noting that with scale comes too much information. It's not easy to recognize anomalies in big data, but Prelert has the machine-learning tool that can do it: it trains its attention to bring the true anomalies to the fore. Its algorithm looks at past trends, and teaches itself to recognize the true anomalies. Prelert's goal is to "tell the story behind advanced threat activity and operations issues."
ProtectWise: retrospective and prospective analysis.
CTO and co-founder Gene Stevens introduced ProtectWise. ProtectWise built the ProtectWise Grid to emphasize pervasive visibility and automated threat detection. Network sensors feed optimized network replay (a "time machine"), and then an enterprise security platform. The time machine for threat detection uses real-time, retrospective, and prospective analysis. It comes with an API that's intended to offer strong integration into the customer's enterprise. In sum, Stevens said, the solution enables cogent reasoning about complex situations.
RiskSense: quantification enables proaction.
Srinivas Mukkamala, CEO of RiskSense described his company and its solutions. Their goal is to identify ("contextualizing external threat data and internal security intelligence"), prioritize ("correlating with business criticality"), and orchestrate responses ("shortening time to remediation"). RiskSense quantifies risk to enable the customer to focus on what's really important. Quantification enables an enterprise to be proactive in how it handles its security. Mukkamala explained that the solution scales: one of the ten largest universities in the United States is using it successfully.
SafeBreach: self-scout through an adversary's eyes.
SafeBreach's CEO, Guy Bejerano, asked the conference to imaging "playing a hacker." He asked how good you thought your security would be if you were hacked. Would it hold up? Not understanding the adversary puts us at a disadvantage. SafeBreach offers a virtual hacker platform that continually validates your controls and enables you to answer the question, "Am I secure?" Don't wait for the attack, he advised. Instead, play the attacker. SafeBreach enables its customers to choose a target, visualize the kill-chain, and then break that chain based on your strengths. SafeBreach's hackers' playbook report also gives insight into the adversary's tactics, techniques, and procedures.
ThreatQuotient: universal threat language turns data into intelligence.
ThreatQuotient CEO John Czupak described his company's approach to making analysts more effective. Too many threat information feeds are siloed to a set of products. And too many sharing platforms simply bring more silos with them. His company's ThreatQ offers a universal threat language. It transforms data into intelligence. Context helps the analysts assess the relevance of the data, ultimately enabling them to anticipate threats. ThreatQ is a threat operations and management system: it includes a threat library, an adaptive workbench, and an open exchange. ThreatQuotient also enjoys a global presence.
Vera: control your data no matter where they are.
Vera's CEO Ajay Arora invited the conference to consider what the ability to monitor and control data wherever they may have gone could mean for security. Vera offers three layers of security: it enables encryption, it enforces access controls, and it provides dynamic data protection. The goal is to make the data as impenetrable as possible in a way that's invisible to legitimate users. This involves establishing dynamic control over what users can do with your data. Vera's solution is frictionless, secure collaboration with partners, affording protection of data at rest, data in use, and data in motion. "We treat the user experience on a par with security."
