Cyber Attacks, Threats, and Vulnerabilities
The Jihadist Threat Won't End With ISIS' Defeat (Foreign Affairs) Numerous additional Salafi jihadist organizations will be ready to take ISIS' place as long as the conditions that gave rise to such groups persist.
In Iraq, the danger of a dormant Islamic State (Chicago Tribune) Remnants of a defeated Islamic State remain in Iraq, posing a danger that neither the U.S. nor Baghdad can ignore.
Russian hackers targeted more than 200 journalists globally (Fifth Domain) The AP identified journalists as the third-largest group on a hacking hit list obtained from cybersecurity firm Secureworks, after diplomatic personnel and U.S. Democrats.
Inside a Russian disinformation campaign in Ukraine in 2014 (Washington Post) Classified report documents six days of an covert influence operation on social media.
WannaCry Ransomware Lives On (But With Less Bite) (News World) WannaCry is still kicking and looking for its next victim, but it's not quite the monster it was earlier this year...
WannaCry Influences Companies to Stock Bitcoin for Ransomware Emergencies (BItcoin News) Ransomware attacks aren't new to the internet. There are recorded instances of such attacks even before Bitcoin came into existence. However, in the recent years, the number of ransomware attacks involving demands for payment in Bitcoin has rocketed through the roof. These incidents, mostly targeting businesses have put many companies on edge, forcing them to invest in Bitcoin as a measure to deal with potential attacks in the future.
North Korea Demands U.S. Prove Ransomware Claim (Time) The U.S. said Pyongyang was behind the WannaCry cyber attack
North Korea vows to retaliate over US ransomware accusation (Fifth Domain) North Korea said Thursday that a U.S. accusation that it was behind a major ransomware attack was a “grave political provocation” and vowed to retaliate.
North Korean Hackers Targeting Individuals: Report (Security Week) North Korean state-sponsored hacking group Lazarus has started targeting individuals and organizations directly, instead of focusing exclusively on spying on financial institutions, Proofpoint reports.
Industry Reactions to U.S. Blaming North Korea for WannaCry (Security Week) The United States, Canada, Japan, Australia and New Zealand have all officially accused North Korea this week of being behind the WannaCry campaign. They join the United Kingdom, which blamed Pyongyang for the attack back in October.
The Opening of the North Korean Mind (Foreign Affairs) Foreign media is trickling in to North Korea, revealing the gap between Pyongyang’s propaganda and reality. The regime is well able to repress subversion in the short term, but over time the flow of outside information may be the best way to help the country evolve.
Should spies use secret software vulnerabilities? (C4ISRNET) It’s a choice of how best to protect the public: Exploit software vulnerabilities to collect intelligence information that may help keep people safe? Or disclose the flaw, letting the software company fix it and protect millions of regular computer users from malicious attacks by hackers?
Immunity's Aitel backflips on WannaCry claims, Kaspersky (iTWire) The head of American security firm Immunity, Dave Aitel, appears to be backtracking on his claims, made in August, that British security researcher Ma...
Printer-spoofing Campaign Installs Espionage-Bent Backdoors Inside the Enterprise (Infosecurity Magazine) There has been an uptick in attacks through Canon, HP and Epson printer and scanner email attachments.
Mirai Variant "Satori" Targets Huawei Routers (Security Week) Hundreds of thousands of attempts to exploit a recently discovered vulnerability in Huawei HG532 home routers have been observed over the past month, Check Point security researchers warn.
Amateur Hacker Behind Satori Botnet (BleepingComputer) A so-called "script kiddie" is behind the recently discovered Satori botnet that has scared security researchers because of its rapid rise to a size of hundreds of thousands of compromised devices.
Hackers take advantage of bitcoin's wild ride (CNNMoney) Bitcoin is booming and so are criminal schemes looking to make money off the trend.
Vulnerability Affects Hundreds of Thousands of IoT Devices (BleepingComputer) Here's something to be cheery on Christmas Day —a vulnerability affecting a web server that's been embedded in hundreds of thousands of IoT devices.
Naval Dome exposes vessel vulnerabilities to cyber attack (Sea Trade) More onboard cyber vulnerability has been revealed, with maritime cyber defence firm Naval Dome demonstrating yet more ways hackers can compromise ship safety.
Windows 10 WARNING - PCs vulnerable to hack after shock security risk discovered (Express.co.uk) WINDOWS 10 users have been put on alert after a shock new security risk was discovered.
Nissan Informing 1.3 Million Canadians of Potential Breach (Digital Guardian) Nissan said Thursday that information belonging to Canadian customers, like their names, addresses, and vehicle identification number, may have been breached.
Security at stake as dark web puts up ransomware for hire (The Times of India) It's becoming easier and more affordable to turn into a cybercriminal.
Julian Assange’s Twitter account goes offline, returns (TechCrunch) It’s a Christmas miracle of sorts. Julian Assange’s Twitter account disappeared from the site, returned, and now there’s a bouncing baby Corgi up top...
US Navy Tweets about Julian Assange after his account disappeared (HackRead) The official Twitter account of WikiLeaks founder Julain Assange disappeared earlier today without any indication.
Navy explains 'inadvertent' tweet about Julian Assange (TheHill) The Navy on Monday sought to explain why it tweeted WikiLeaks founder Julian Assange's name, attributing it to an "inadvertent keystroke."
Cyber Trends
2018 will be the year of cyberwar (Macleans.ca) The cyberattacks of the past year can only hint at the coming weaponization of security flaws
Lessons learned from 2017 cybersecurity incidents (SearchCIO) From the Equifax data breach to the WannaCry ransomware attacks, here's a SearchCIO rundown of the five cybersecurity incidents that had the most impact in 2017.
Cybersecurity Predictions From ZeroFOX And Dyadic (Information Security Buzz) James C. Foster, CEO at ZeroFOX, a social media security firm based in Baltimore, give his insight about social media next year. James C. Foster, CEO at ZeroFOX: Social media will be the number one vehicle for ransomware distribution in 2018. Currently, there are nearly one million social media accounts compromised every day, and that number will continue to …
Security in IoT space to be of prime focus in 2018, say experts (The Financial Express) Amid a rise in cyber attacks across the world, ensuring the security of devices linked to the Internet of Things (IoT) ecosystem will be a key focus of companies in 2018, say experts.
While Blaming Companies for Breaches, Consumers Aren't Prioritizing Their Own Security (eSecurity Planet) Just 25 percent of U.S. consumers use two-factor authentication, and just 45 percent use a PIN to protect their mobile device.
Iran industrial cyber system among world's 10 most vulnerable (Mehr News Agency) TEHRAN, Dec. 24 (MNA) – The findings of a research by Kaspersky Lab shows that in the first 6 months of 2017, Iran has been among 10 countries whose industrial cyber systems are the most vulnerable.
Top Canadian cyber security stories of 2017 (IT World Canada) Equifax. In one word that sums up the terrible year in cyber security 2017 has been. Wannacry ransomware, which briefly spread in
Marketplace
The economics of cybersecurity (SC Media US) 2017 saw the rise of economic initiatives intending to boost and benefit from cybersecurity.
The professional cybersecurity groups (SC Media US) As cybersecurity has grown in importance within organizations, professional development has become a greater priority. These groups stand out as they educate and elucidate.
Cryptocurrency 101 and Is Bitcoin a bubble? (The Commentator) The questions on everyone’s mind the past few weeks has been – is Bitcoin a bubble? If it’s a bubble, when will it burst? If it’s not, is it too late to invest? Of course, there are no definite answers to the questions aforementioned. However, this article will attempt to shed some light onto the …
7 reasons why you must embrace the cryptocurrency wave (YourStory.com) Cryptocurrency is a form of digital asset developed to authorise transactions of money online. It emerged after the creation of Bitcoin in 2009. Since cryptocurrency is a virtual currency associated w...
The Kaspersky Lab-U.S. government fight removed a miniscule amount of business (Cyberscoop) Kaspersky's business with the U.S. government wildly pales in comparison to its competitors.
Cyber Surveillance Firm Founder Defends Company’s Practices (CTECH) Co-founder of NSO Group whose products were tied to government spying on journalists and dissidents defended the company’s ethical standards in a rare interview
Where Will Check Point Software Technologies Be in 5 Years? (The Motley Fool) The cybersecurity provider’s business model makes predicting its future easier than you may think.
Products, Services, and Solutions
5 best website scanner tools to detect malware before it strikes (Windows Report) Even if you know and follow all the necessary security measures on your own when you’re managing your website, you will never be able to …
Edward Snowden’s new app turns any Android phone into a surveillance system (TechCrunch) NSA Whistleblower Edward Snowden is among the backers of a new surveillance app that helps guard against computer hijackings. Haven is an open source app..
Snowden's new app protects you from kidnappers. Or maids. (CNET) Haven, an app backed by Edward Snowden, is like a baby monitor on steroids. Or the world's most paranoid nanny-cam.
Greater Integration Between Incident Response Teams Now Possible with PhishMe Triage (markets.businessinsider.com) There is a heated debate taking place as to how Artificial Intelligence (AI) will impact the workforce. While these two sides battle it out, some of the giants in tech as well as other industries are gobbling up AI startups at a record pace.
Apple admits to slowing iPhones, you’re not imagining it (Naked Security) Apple has quietly been suppressing the CPU speed of older iPhones to stop their batteries randomly shutting off
Technologies, Techniques, and Standards
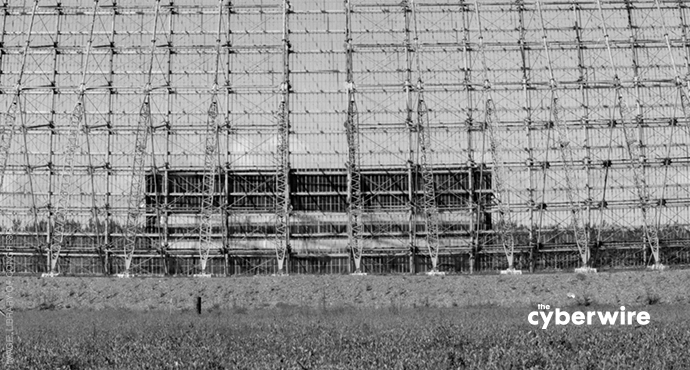
Russia is pushing the Army to move faster on electronic warfare (C4ISRNET) The Army believes it can accelerate the development of a key electronic warfare program, and in the process, provide a road map for how the service might improve acquisition.
Seven Seas Cybersecurity: Captain, We Have a Problem (Security Week) Detecting compromises requires monitoring a series of activities over time
Two Can Play at that Game: Thinking Like a Malicious Adversary (BlueCat) If you don’t know what you’re fighting, how can you expect to fight it? This whiteboard session delves into the criticality of DNS in developing a cyber security counter-strategy. Keep malicious adversaries in mind when structuring your domains and your network will be robust enough to battle them.
Design and Innovation
Here’s What is Limiting Blockchain Mainstream Use (InfoQ) In a recent article on Medium, Blockchain engineer Preethi Kasireddy describes the key challenges that Blockchain has to overcome to become practical for mainstream use.
Elon Musk Is Now Linked to the Mystery of Who Invented Bitcoin (Big Think) Did Elon Musk invent Bitcoin? The mystery surrounding the creator of the world's most popular cryptocurrency deepens.
Research and Development
Researchers: Artificial Intelligence is dumber than a 5-year-old and no smarter than a rat (Tech Startups) We’ve all heard or read about how robots are going to take away our jobs. Saudi Arabia even went as far as granting citizenship to “Sophia the robot” back in October (See the video below). With crytocurrency at the top …
Silicon Valley Is Turning Into Its Own Worst Fear (BuzzFeed) We asked a group of writers to consider the forces that have shaped our lives in 2017. Here, science fiction writer Ted Chiang looks at capitalism, Silicon Valley, and its fear of superintelligent AI.
Proof of randomness builds future of digital security (Phys.org) In an effort to block emerging threats to online security, researchers at Princeton University have developed a method to verify the strength of random number generators that form the basis of most encryption systems.
Gaming Disorder Soon To Be Classified As Mental Health Condition (Tech Times) Gaming disorder will be included in the upcoming edition of the International Classification of Diseases by the World Health Organization. What are the symptoms of a gaming disorder, and is it even legitimate?
Legislation, Policy, and Regulation
China aims to become world-leading cyber power by 2035 (Xinhua) China will advance the development of information technology and spread internet applications in coming years, with the aim of becoming a world-leading cyber power by 2035, a senior official said Monday.
Cyber to be the Weapon of Choice for Developing Countries, Says Former Mossad Chief (CTECH) Developing countries would move to adopt cyber attacks as a way to disrupt democracies, retired Mossad Director Tamir Pardo said at a conference
“Risk Informed, But Not Risk Averse”: the National Security Strategy Approach to Cyber Ops (Just Security) The Trump administration’s National Security Strategy (NSS) is replete with references to cyber operations and their impact on national security.
Opinion | Congress shouldn’t let this crucial surveillance program lapse (Washington Post) Reform it — don’t allow it to expire.
Commentary: In democracies, voters warm to secret services (Reuters) In the early hours of Tuesday in the northern UK cities of Sheffield and Chesterfield, armed police blew open doors of homes and a Muslim community center, arresting four men aged between 22 and 41. Scanty information given to the news media spoke of a planned “Christmas bomb attack,” now presumably averted. The police, it emerged, were acting on information given by the secret services, probably the domestic service, MI5.
Bill could let cyber spy agency launch attacks with minimal oversight: report (CTVNews) Canada's cybersecurity agency is poised to receive new powers with minimal oversight under a proposed piece of federal legislation, a report released earlier this week is cautioning
Cyberspace: Israel's Next-Generation Battlefield Today (The Media Line) The country is targeted by approximately 1,000 cyber-attacks …
GCHQ 'over-achieved' in hunt for exploits and cyber weapons (ZDNet) But hiring and keeping staff remains a challenge.
Boris Johnson confronts Moscow over allegations of Brexit meddling (The Telegraph) Boris Johnson's visit to Moscow descended into a slanging match as the Russians accused him of "making up" allegations of Brexit meddling in an ugly public disagreement.
Johnson urges better Russia relations (BBC News) Boris Johnson and Sergei Lavrov clash over cyber-attacks but also trade jokes after talks in Moscow.
Revisions to Wassenaar cyber export-control agreement gain industry support (Inside Cybersecurity) International negotiators made changes to an arms-control agreement that for years had troubled U.S. tech companies -- which argued the export controls could undermine cybersecurity improvements -- with the latest revisions drawing industry applause as well as calls for additional changes.
How do you change the most important law in Internet history? Carefully (Ars Technica) Op-ed: Changes to law shielding websites from liability for user posts should be minor.
Congress Is Debating Warrantless Surveillance in the Dark (WIRED) As the debate over Section 702 continues, those deciding its fate don't know basic facts about how it works.
Cyber legislation is teed up for action in 2018, if Congress can find the time (Washington Examiner) Congress faces a compressed election-year calendar, although data-breach legislation seems likely to get attention starting this winter.
Bill ropes in key players for defence (The Straits Times) A proposed Bill for cyber security will be tabled in Parliament for debate next year to shore up Singapore's defence against rising threats, many of which are state-sponsored.. Read more at straitstimes.com.
Litigation, Investigation, and Law Enforcement
Lizard Squad and PoodleCorp Hacker Pleads Guilty to DDoS Attacks (BleepingComputer) A member of the infamous Lizard Squad and PoodleCorp hacking groups pleaded guilty this week to charges of running a DDoS-for-hire platform that he and others used to launch DDoS attacks on targets across the globe.
Damian Green accused of ‘dirty tricks’ over leaked text messages (Times) Damian Green was accused of a new “dirty tricks” campaign last night after text messages he exchanged with the woman who accused him of sexual misconduct were leaked to the media. The former first...
Christopher Steele hedges on Russia dossier claims against Donald Trump (The Washington Times) Christopher Steele, the former British spy who fueled an ongoing investigation into President Trump’s administration, was a lot more confident of his charges when he wrote his now-notorious 2016 dossier than he is today in defending it in a libel lawsuit.
Feds Say Phoenix Men Wanted to Sell Honeywell Secrets to Cartels; Now One Is Dead (Phoenix New Times) Family and friends have been spreading all kinds of theories about how Robert Jeremy Miller died but there remain more questions than hard facts.
Man Threatened Company with Cyber Attack to Fire Employee and Hire Him Instead (BleepingComputer) A North Carolina judge sentenced a Washington man this week to 37 months in prison for threatening a company with attacks unless they fire one of their employees and hire him instead.
Guide to Negotiating an IP Infringement Indemnity (Galkin Law) Licensors and vendors of software and SaaS offerings should pay close attention to the intellectual property indemnification clauses in their customer agreements.