Cybercrime as a business.
Black markets and those who work in them have clear economic motives, and they're paying attention to industrial control systems. The first thing to understand about the black markets is that they function as markets.
The Darknet and those who trade there.
Bruce Billedeaux, Senior Consultant at Maverick Technologies, offered a guide to the Darknet that sought to demystify it for an audience interested in the security of industrial control systems. He characterized the Darknet as comprised of those things accessible from a TOR browser. TOR, Billedeaux explained, is maintained by tens of thousands of volunteers around the world. It runs on the Onion Protocol, and it places layers of router keys around an encrypted message. Should you wish to visit the Darknet (which Billedeaux advised against) you may do so by running TOR in a virtual machine.
Not everything on the Darknet is nefarious. Much of its content, for example, involves dissident political speech conducted where repressive regimes are less likely to find the speakers. Some Darknet content amounts to a goof, like guides to steam tunnels under university campuses. But the Darknet is also the home to a big black market that includes contraband souks, a shadow banking community, even well-reviewed escrow services.
For the ICS security community, the most interesting nefarious content traded on the Darknet includes hacking tools, products, and services, all of which have had the effect of commodifying cyberattacks. These products and services are easily accessible to criminals, hacktivists, and disgruntled insiders. Using these commodities requires little knowledge, and their prices are well within the range of what people in the market are able to pay.
Most malware is targeted against Windows machines, and ICS remains overwhelmingly dependent upon Windows, Billedeaux observed. Ransomware has grown more sophisticated--for example, it now excludes OS files but encrypts everything else, thus ensuring that the host will continue to operate, and that the victim will therefore receive the ransom message.
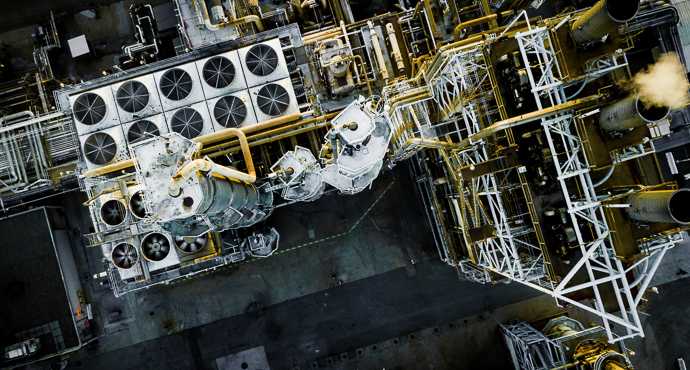
ICS systems are increasingly of direct interest to criminals, particularly those interested in extortion or cryptojacking. But there remains also a problem of collateral damage from attacks not originally targeting industrial systems. The potential income from ransom attacks or cryptojacking has encouraged distribution of malicious code into the wild, thus raising the risk of all connected systems. A particular risk to ICS security, Billedeaux said, was password reuse and exposure that practice brings to credential-stuffing attacks.
Discouragingly, Billedeaux suggested that industry shouldn't expect too much help from law enforcement. He cited the case of the three-hundred people arrested last week for Darkweb child porn. That’s what law enforcement is worried about, he said, not ICS hacking. Furthermore, takedowns of malicious Darknet enterprises tend to be of temporary value. "The Silk Road takedown was a whack-a-mole," as he put it. That very large contraband vendor was succeeded by a growing number of smaller vendors. We should expect another cycle of consolidation until a market gets big enough for the authorities to take notice and crush it. And then the process will begin again. This, Billedeaux concluded, is the Darknet business cycle, and that cycle affects the ICS space.
The mind of the hacker and why it matters.
Understanding how cybercriminals think will help organizations defend themselves. Evan O’Regan, Head of Connected Additive Manufacturing at Irdeto explained that the industrialized hackers' business model defines their tactics. They're interested in, obviously, making money, and in doing so they work to increase their return on investment. They work to increase revenue, cut costs, and benefit from automation to scale with less expense.
IoT cyberattacks have become the norm, O'Regan said, but the security mindset hasn't. This is particularly troubling in the light of the normal failure that attends increasingly complex systems. O'Regan recommended reframing the problem to make it more manageable. That will lead organizations to defend their "high-impact points" first. It will also lead you to start small, where you can have a measurable effect on security.
As an organization's security matures, it should cut into the attacker's business. It should also bring about a change in organizational culture. An alert, resolute organization is a harder target, and one that presents the criminal with an unpromising return on investment.
