Policy, conflict, attribution, and preparing for more to come.
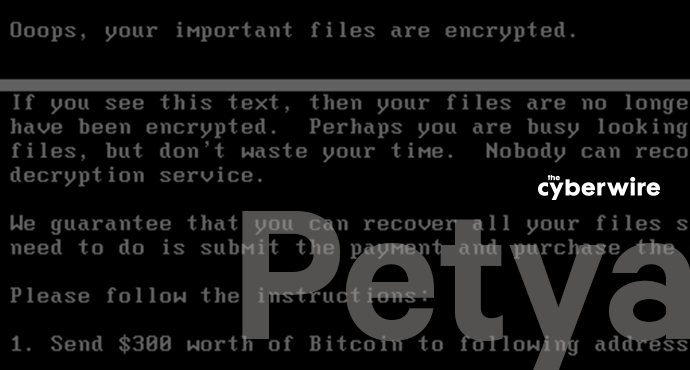
It's too early for firm attribution of the Petya-based pandemic (although Ukrainian authorities are looking at their big and unfriendly neighbor Russia), but the outbreak does have policy implications.
First, it incorporated an exploit, EternalBlue, whose leakers (the ShadowBrokers) claim was stolen from the US NSA. So the loss of code by an intelligence agency, if that indeed is what happened, and most observers think it is, is having a significant global effect. There will be renewed calls for explanations of how such tools are developed, disclosed, and secured. A case will be made that they should be controlled as closely as kinetic weapons are. (But it will be tougher to lock up code than it is to keep automatic weapons behind bars closed with a Series 200 lock.)
Second, assuming that EternalBlue is an NSA exploit, it seems unlikely that it leaked without the work of a hostile intelligence service. The initial outbreak in Ukraine also suggests Russian activity.
Third, the consequences of this Petya outbreak have fallen heavily on operators. The effects on shipping, energy distribution, and medical care are a good bit closer to kinetic effects than are the encrypted files conventional criminal extortion attempts leave in their wake.
Finally, as was the case with WannaCry, the people behind the attack are asking for ransom, but they're not receiving very much. In WannaCry that may have been due to botched Bitcoin wallet configuration, but that isn't the case with the current Petya version. Their take late Tuesday was pegged at no more than about $7000, which is paltry, given the scope of the infection. So it's natural to entertain the possibility that the campaign's principal goal is either disruption, misdirection, or staging. These are more consistent with state than criminal activity.
Update: 6.30.17: While the putative ransom note's text appeared in English, Ukrainian authorities blame Russian hackers and call the attack misdirection for malware installation (Reuters). The researcher known as the grugq has a clear analysis of what's up in Medium; he calls the relationship to Petya "skin-deep," and sees misdirection, not extortion. Petya's author, who hawked the ransomware in dark web souks during 2016 and goes by the nom-de-hack "Janus," substantially agrees, and (for what it's worth) says he'd like to help (Daily Beast). Caveat emptor. There's another interesting development: F-Secure says it's found signs EternalBlue was incorporated into Petya/Nyetya/NotPetya six months ago, that is, before the ShadowBrokers dumped the exploit, which suggests the authors are either close to the Brokers (perhaps as suppliers, or perhaps they are the Brokers) or that they had independent access to the exploit (Computing).
Attribution: circumstance and motivation.
Barrett Lyon, Head of R&D at Neustar Security Solutions, commented on what this means for the near future. "It’s going to continue to happen and get worse," he said. "Thanks to state sponsored offensive cyber security efforts, we’re seeing very complex attacks leaked and handed over to the common thief to leverage. I do find it a little curious how it breaks out in specific regions, though."
As far as attribution is concerned, it will prove circumstantial and murky, and consensus will emerge only at the end of a long process of investigation. Mark McArdle, eSentire CTO, reminds us that attribution of attacks is notoriously difficult. “Finding irrefutable evidence that links an attacker to an attack is virtually unattainable, so everything boils down to assumptions and judgment," he said, and goes on to suggest that visibility into an enterprise's networks is more important than ever.
Nozomi Networks CEO Edgard Capdevielle sees the incident as consistent with a long-standing pattern of attacks that begin by hitting Ukrainian assets, “The Ukraine continues to be in the cross-hairs of persistent cyber attackers. Whether you believe the Ukraine is a test-bed for nation state aggression or an issue between two specific countries, the continued barrage of attacks against Ukrainian infrastructure is disturbing."
Capdevielle also notes that, while initial reports suggested the effects were being felt in IT systems, OT and ICS were also vulnerable. "Critical infrastructure provides around the globe should re-double their efforts ensure proper separation of their IT and OT networks and be actively monitoring their ICS environments and applying advanced anomaly detection systems so that they can detect and remediate any efforts to disruption operations of ICS within their critical infrastructure.”
Prospects for future attacks.
Ryan Wilk, Vice President, Customer Success, at NuData Security, commented that the Petya campaign is a foreseeable sequel to WannaCry. “Last month’s WannaCry attack likely emboldened cybercriminals worldwide," he said. "Petrwrap [an alternative name for this version of Petya] is another example of how pervasive the malware problem has become." He advocates designing and building systems "from the ground up" that protect users and data through passive biometrics and behavioral analytics.
Mike Shultz, CEO of Cybernance, warned that the incident represents an escalation of risk. "This marks yet another crime scene with substantial evidence that global economies are at massive risk because of 1) the reliance on connected devices and computers, and 2) the lack of government-mandated and incentivized cyber defense for both public and private sectors." He sees economic damage as a likely motive, and strongly urges the C-suites responsible for business to take their security seriously.
Policy: incentives, regulation, and a whole-of-nation approach.
Shultz sees three ways the US in particular should address this kind of threat (advice to other countries would, presumably, be similar):
"Mandates and incentives." Shultz thinks the recent Cybersecurity of Federal Networks Executive Order is on the right path, and he also thinks the New York State Department of Financial Services' cybersecurity regulations for financial services also represent a step in the right direction. Enterprises should also take advantage of the liability protections in the SAFETY Act, as administered by the US Department of Homeland Security. "The federal government must do better to incentivize these mandates and protections, all while balancing a general aversion to government regulation from some industries, like utilities and energy."
"Accountability." Shultz thinks mandatory compliance ought to replace the largely voluntary regimes we've seen in the past.
"Streamline protection of the whole, not just the parts." Interconnection requires a whole-of-nation approach to security. "The U.S. needs to find a balance between public and private sector cybersecurity regulation, where a consistent and unified defense program can be referenced, implemented, measured, and maintained across agencies, enterprises and individuals. All parts pose risks to the whole,” Shultz said.