A realistic appraisal of conflict in cyberspace.
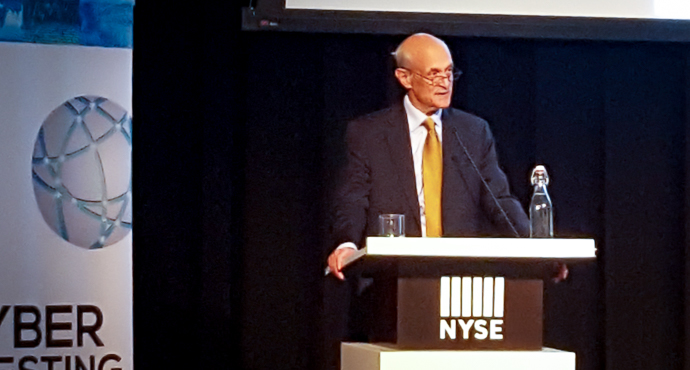
Michael Chertoff, former US Secretary of Homeland Security and now Executive Chair of the Chertoff Group, began his keynote with a quiet appeal for thoughts on behalf of the victims of the Manchester bombing, which he suggested is a sad reminder that we do face "a struggle against evil."
Some of that struggle, of course, is conducted in cyberspace. The difficulties we face there have their roots in the original design of the Internet. This was, Chertoff noted, essentially a resilience model of communication among trusted parties—laboratories and Government agencies—and it was build without considering the security of a network to which untrusted parties would have access.
We've seen in recent years, he said, not only an uptick in the scope, significance, and consequence of cyberattacks, but also a great deal of increased cooperation among governments and criminal organizations.
We also see the dangers of illicit activity in other areas. Chertoff noted that the recent WannaCry incident showed the risks that pirated software, which is usually also unpatched and outdated software, can pose to the entire Internet.
Part of the struggle against cybercrime is legal, and he noted with approval the US indictment of Russian criminals and intelligence officers in the notorious Yahoo credential breach. It's unlikely in the extreme that those indicted will be handed over to US authorities, but the indictments do have a chilling, inhibitory effect on gangs and foreign intelligence services.
Speaking as he was on Wall Street, Chertoff noted that financial services are attractive to hackers in all sort of ways, and that the global financial system, as well protected as it may be, is nonetheless exposed to considerable risk. Threats to the integrity of financial data constitute a serious risk to national security as well as well as to banks and other financial service providers. The financial sector is acutely aware of centrality of cyber threats, and Chertoff, after a quick review of attacks that sector has recently sustained, drew the lesson that the response should be "multi-faceted management of risk." And this should be done with the understanding that risk can only be managed, not eliminated.
Technology is part of the solution, but he also said that WannaCry has shown that people don't take the easy and obvious steps to protect themselves. He commended multiple-factor authentication as an important safeguard, but stressed that enterprises need to think through what those factors should be, and how they should be implemented.
Behavioral monitoring on the network is an increasingly important third security measure. Here as elsewhere technology helps focus human attention. Long-term behavioral monitoring and analysis will flag anomalies for deeper inspection. Edward Snowden, Chertoff said, showed that the biggest threat isn't a hole in a firewall, but rather a rogue insider.
Encryption, backup, and crisis response round out the measures Chertoff commended to the conference.
He closed with a set of warnings. First, third-party dependencies require inspection and attention. Second, everything, with the Internet-of-things, is becoming smart and connected. Yet these things are not yet secure, and so "We need to start thinking how we build security into the IoT."
Finally, he asked how we might address the concern that the global financial system could become a battlefield in cyberwar. He strongly advocates building international norms of conflict that place the financial system off-limits to cyberwar. This is a humanitarian issue as important as others that the laws of armed conflict have addressed.
Video of his presentation may be found here.