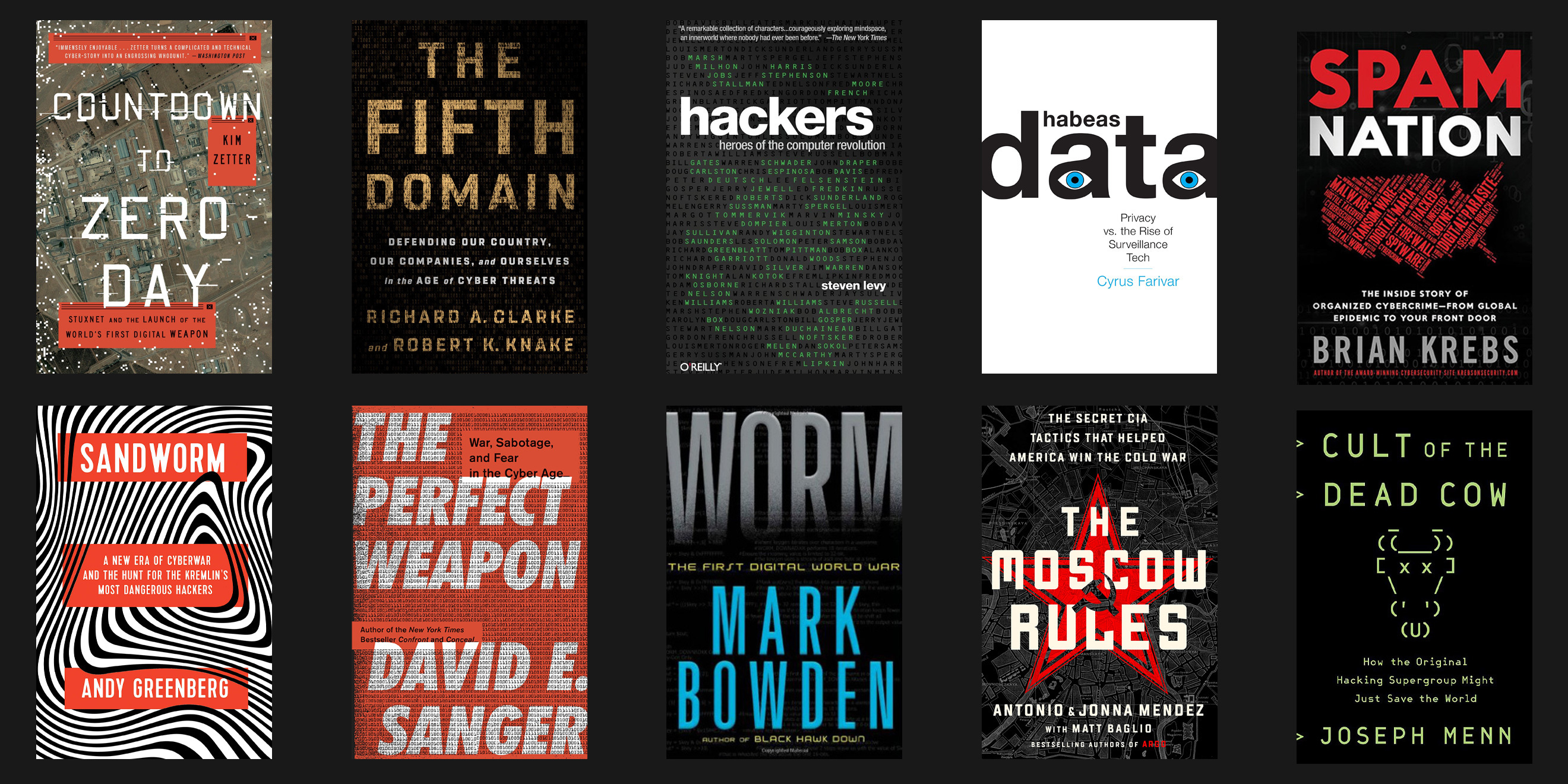
Our 10 favorite non-fiction cybersecurity books.
Our own CSO and Chief Analyst, Rick Howard recently told us all about his favorite cybersecurity novels in his CSO Perspectives article and podcast, Four cybersecurity novels to distract you from the current zombie apocalypse. Rick’s thoughts sparked a lot of conversation among the team about the books we liked and those we didn’t. And we figured our readers might like to hear about our favorites and tell us about theirs. Our list is below, along with some brief comments from the team members that selected it: Peter Kilpe, Rick Howard, Jen Eiben, and Dave Bittner.
We’d love to hear what’s on your library shelves too. If you have additional recommendations, or your own thoughts on the books we’ve talked about, please let us know on Twitter, Facebook, or LinkedIn.
Countdown to Zero Day: Stuxnet and the Launch of the World's First Digital Weapon.
by Kim Zetter.
Kilpe: Zetter’s Countdown to Zero Day is a must-read for anyone interested in ICS security. Superbly researched, this gripping read about Stuxnet is interwoven with a thought-provoking history lesson about these kinds of attacks and their implications for the future. I found this book hard to put down, and its story sticks with me as we watch that future unfold.
Bittner: The story of Stuxnet is an inflection point in the history of cybersecurity, and Kim Zetter weaves the tale in a compelling, captivating way.
Published 2014 by Crown | Goodreads
Cult of the Dead Cow: How the Original Hacking Supergroup Might Just Save the World.
by Joseph Menn
Howard: On the surface, it is a remembrance of a fascinating time in cybersecurity history, early 1980s to mid-2000s, when the world transitioned from dial-up modems to the beginnings of what the internet is today, when the term “hacker” identified clever people who were interested in how the world works, and when Gen Xers were old enough to understand what their baby boomer parents did in the 1960s and were eager to see what they could do in the exponentially expanding digital age. If that was all the book was, it would be a worthwhile read. But Joe has something bigger in mind. Joe has noticed a missing element in “Big Tech” thinking as companies like Google and Facebook have grown to dominate the world’s culture. He believes that “Big Tech” doesn’t consider even basic ethics when they make decisions to drive the growth of their companies. He hopes that by describing the maturity journey of the cDc, from internet pranksters to seasoned and respected graybeards, that these new millennials, born between early 2000s and present day, and now in charge of “Big Tech” might use that journey as a blueprint to guide them in the future.
Published 2019 by PublicAffairs | Goodreads
CyberWire Interviews: 7.26.19, 7.28.19
The Fifth Domain: Defending Our Country, Our Companies, and Ourselves in the Age of Cyber Threats.
by Richard A. Clarke, Robert K Knake.
Howard: The authors reiterate that we need to shift the balance of power from the attacker to the defender, to enable our institutions to be resilient in the face of changing attack patterns. It provides an overview of the developments within ”fifth domain, and describes what has happened in the past with attacks like Stuxnet and Wannacry. The authors note that, while cyber may be the “fifth domain” of war, it is the only domain that is man-made, and therefore we are capable of changing it. They also detail cyber events and actors that are not always well-known.
Published 2019 by Penguin Press | Goodreads
CyberWire Interviews: 7.21.19
Habeas Data: Privacy vs. the Rise of Surveillance Tech.
by Cyrus Farivar
Bittner: Cyrus Farivar has been on the leading edge of privacy and security policy reporting for years, and this book brings together a valuable collection of thought-provoking insights on our willingness to trade privacy for convenience.
Published 2018 by Melville House | Goodreads
CyberWire Interviews: 5.11.18
Hackers: Heroes of the Computer Revolution.
by Steven Levy
Bittner: In order to understand how we got here, we need to know where we came from. Levy chronicles the history of computing and the cast of characters who made it all possible.
Published 2001 by Penguin Press | Goodreads
The Moscow Rules: The Secret CIA Tactics That Helped America Win the Cold War.
by Antonio J Mendez, Antonio Méndez, Jonna Méndez
Eiben: As a student of the Cold War in grad school (Russian and East European Studies concentration), this was a great read. I enjoyed getting a first-hand look at the espionage techniques and gadgets that existed back in the KGB days in Russia and how Tony and Jonna were involved in the rules that CIA agents worked within there. I also like how it’s structured with one of the Moscow Rules highlighted per chapter. It’s easy to see how you can carry the lessons learned to present day social engineering, security and international relations. I was also lucky enough to pick my copy up at the Spy Museum with Jonna herself!
Published 2019 by PublicAffairs | Goodreads
The Perfect Weapon: War, Sabotage, and Fear in the Cyber Age.
by David E. Sanger
Kilpe: This remarkable book not only chronicles the rise of cyberweapons, but adeptly threads together the stories of landmark breaches and cyber attacks, putting them into context with the technological and political forces that are shaping our world. Highly recommended for the seasoned pro and industry newcomer alike.
Howard: The Perfect Weapon changes our thinking from the possibility of an all out cyber war to what has really been going on for the past decade, a continuous low-level cyber conflict between Russia, China, North Korea, Iran, and the United States. These conflicts are designed to walk right up to the line where nations would consider using physical assets to deter enemies but not go over and they cover the gambit of crime, espionage, and sabotage.
Published 2018 by Crown | Goodreads
CyberWire Interviews: 12.7.18
Sandworm: A New Era of Cyberwar and the Hunt for the Kremlin's Most Dangerous Hackers.
by Andy Greenberg
Kilpe: Sandworm is one of those rare books that brings together extraordinary investigative journalism with absorbing narrative storytelling. This tale of mystery and intrigue kept me reading until the wee hours every night. It’s a story I thought I knew, but building on his earlier writing and research on the subject, Greenberg’s book gave me a richer picture of the interconnected people, places, and events in one of the seminal stories of cybersecurity. Details about malware, threat actors, and economic impacts are all there, but it’s the vivid human stories of NotPetya—the people trying to figure out what went wrong, those struggling to get their businesses back up and running in the earliest hours of the attack, catastrophic impacts to hospitals—left a lasting impression on me.
Howard: The story of NotPetya and the Russian role in manipulating foreign governments and sparking chaos globally. It reveals the realities not just of Russia’s global digital offensive, but the characteristics of an era where warfare ceases to be waged on the battlefield and where the line between digital and physical conflict begins to blur.
Published 2019 by Penguin Press | Goodreads
CyberWire Interviews: 11.8.19, 11.11.19
Spam Nation: The Inside Story of Organized Cybercrime — from Global Epidemic to Your Front Door.
by Brian Krebs
Kilpe: There's no better window into the criminal underworld of spammers, than Spam Nation. I confess, I had not really given a lot of thought to spam, thinking it was more of a digital nuisance than anything else, but the fascinating story of the people and organizations behind it all really opened my eyes. This is one of the foundational stories in cybersecurity and vividly illustrates connections between the spammers and threats and threat actors making headlines today. Kreb’s book contains extraordinary, sometimes frightening details on how this underground economy works, the larger than life personalities driving it. It is also a reminder of the risks journalists take to bring us important stories.
Published 2014 by Sourcebooks | Goodreads
Worm: The First Digital World War.
by Mark Bowden
Kilpe: Bowden’s story of Conficker is one of the most accessible and enjoyable cybersecurity books you will find on the shelves at the Cyberwire. It’s a thrilling history lesson that’s as relevant today as it was when it first came out nearly a decade ago. I was particularly drawn in by the stories of how the infosec community began to self organize around the high-stakes problem of Conficker and botnets. Worm chronicles the fascinating cast of real-life characters collaborating and clashing as they sought solutions and navigated extraordinary obstacles.
Published 2011 by Atlantic Monthly Press | Goodreads
