Decrypting ransomware for good.
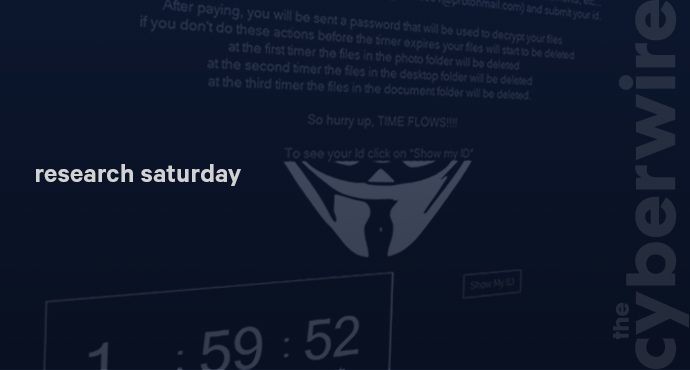
Michael Gillespie is a programmer at Emsisoft, as well as a host of the popular ID Ransomware web site that helps victims identify what strain of ransomware they may have been infected with, and what decryptors may be available. He's written many decryptors himself, most recently for the Syrk strain of ransomware.
Links to the research and Michael's work:



