A rough year ahead for ransomware attacks - and how to stop them.
Dave Bittner: [00:00:03] Hello everyone, and welcome to the CyberWire's Research Saturday, presented by Juniper Networks. I'm Dave Bittner, and this is our weekly conversation with researchers and analysts tracking down threats and vulnerabilities, solving some of the hard problems of protecting ourselves in a rapidly evolving cyberspace. Thanks for joining us.
Dave Bittner: [00:00:25] And now a quick word about our sponsor, Juniper Networks. NSS Labs gave Juniper its highest rating of "Recommended" in its 2019 Data Center Security Gateway Test. To get your copy of the NSS Labs report, visit juniper.net/SecureDC, or connect with Juniper on Twitter or Facebook. That's juniper.net/SecureDC. And we thank Juniper for making it possible to bring you Research Saturday.
Dave Bittner: [00:00:55] Thanks also to our sponsor, Enveil, whose revolutionary ZeroReveal solution closes the last gap in data security: protecting data in use. It's the industry's first and only scalable commercial solution enabling data to remain encrypted throughout the entire processing lifecycle. Imagine being able to analyze, search, and perform calculations on sensitive data, all without ever decrypting anything – all without the risks of theft or inadvertent exposure. What was once only theoretical is now possible with Enveil. Learn more at enveil.com.
Allan Liska: [00:01:34] We've seen an overall shift over the last few years from a focus on widespread consumer-focused attacks to much more targeted business- or organizational-focused attacks.
Dave Bittner: [00:01:49] That's Allan Liska. He's a Senior Analyst at Recorded Future and co-author of the book "Ransomware." The research we're discussing today is titled, "5 Ransomware Trends to Watch in 2020."
Allan Liska: [00:02:03] With that, we've also seen a huge increase in ransom demands from, you know, a few hundred dollars to a hundred thousand, a million dollars, et cetera. So we're seeing a lot of six- and seven-figure ransom demands now. So that's kind of where we see the biggest trend. And then you add to that that the ransomware actors – the more advanced ones – are figuring out other ways to monetize their attacks. So that's where we start to see more of these extortion attacks, where if you don't pay the ransom, then they're going to publish the files they've stolen from your network, you know, and keep them up on a web page somewhere until you pay that extortion fee.
Dave Bittner: [00:02:51] Hmm. It's interesting to me that, you know – I want to say a year ago or so, maybe a little longer than that, we thought we were going to see a shift to cryptomining and that ransomware was going to die down. That didn't play out.
Allan Liska: [00:03:04] No. So, in 2017, we saw a huge dip in ransomware attacks. And then there was an acceleration of cryptomining attacks. And that continued, to your timeline, through a good part of 2018. It turns out it's really hard to make money cryptomining. Unless you're able to command literally hundreds of thousands and maybe even millions of devices to do the mining for you, it's actually really hard to make any kind of substantial money from cryptomining. Even as Bitcoin and other cryptocurrencies were rising, it was just that much more difficult to actually do the calculations at scale.
Dave Bittner: [00:03:51] What other trends are you tracking here when it comes to ransomware?
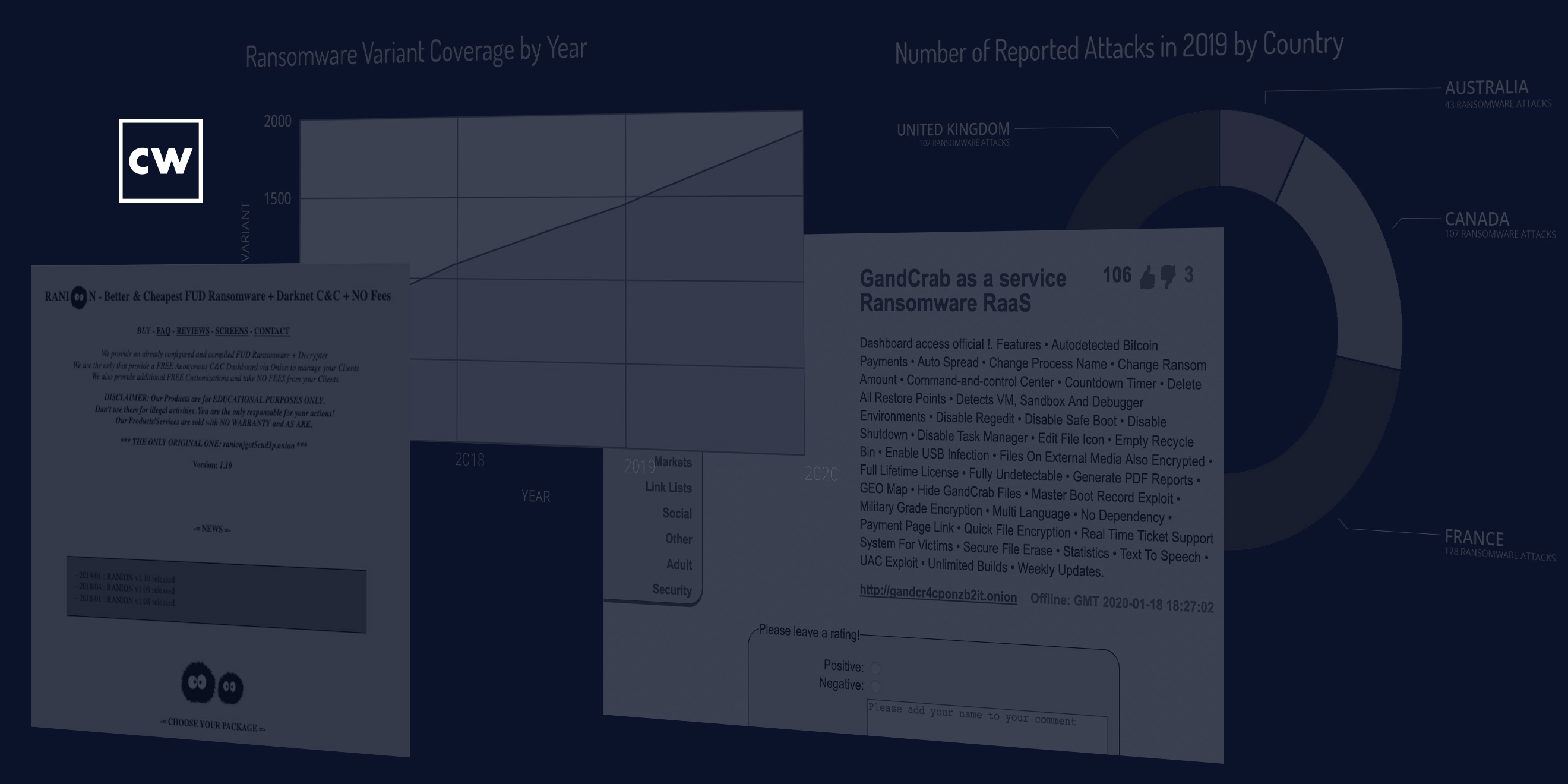
Allan Liska: [00:03:55] So, we're seeing a big rise in ransomware-as-a-service, which is really interesting because some of the top ransomware actors – so, the teams behind REvil, also known as Sodinokibi, and Nemty, MegaCortex – all rely on a ransomware-as-a-service model. And of course, famously, before they were shut down, GandCrab relied on that model as well. What that does is it becomes a force multiplier for the threat actor. Instead of having to worry about a dozen threat actors, we now have to worry about hundreds of threat actors. Still only dozens of ransomware that are really a threat, but there are a lot more people behind them using a lot of different methods of activity, which means that it's harder to pinpoint where the entry point for the ransomware will be.
Allan Liska: [00:04:53] So, if you take REvil, for example, primarily, what we used to see is they would be delivered through phishing emails – and we still see a lot of that – but some of the people that use their ransomware-as-a-service will also gain access through a managed service provider, and then they'll jump from that managed service provider to target customers. We saw that in Texas, for example, last year, with the twenty-two towns and cities that were infected from a managed service provider. We've also seen some of the REvil affiliates who are going after Citrix vulnerabilities or Remote Desktop Protocol, et cetera. Which means that that, again, that attack surface grows because there are so many different threat actors that are using that same ransomware.
Dave Bittner: [00:05:49] Given where we stand today with ransomware, what are your recommendations for organizations to set up shop to be protected against it? In this environment, as things have evolved, how do you think folks should go about that?
Allan Liska: [00:06:04] Well, one of the things that you need to worry about – we've always advocated for good backups, right? Good backups and checking those backups and making sure that you have offline access to your backups, that they're not directly connected to the networks because we know attackers, ransomware actors like to go after those backups.
Allan Liska: [00:06:26] But the other thing that you now have to worry about is you have to identify the attack as soon as possible. So, before, what you'd have is you'd have – when I say "before," I'm talking all the way back in 2016, 2017, you know, the ancient times...
Dave Bittner: [00:06:46] (Laughs)
Allan Liska: [00:06:46] ...You'd have the ransomware actor who would gain access to a box and then they'd infect that box and then the attack would be over. With the more advanced ransomware actors that we're seeing a lot of activity from now, they're sitting in the network for a couple of weeks, they're learning the network, they're understanding it, and they're deploying the ransomware after they've studied the network.
Allan Liska: [00:07:10] Which means that early detection is much more important, because in addition to studying and learning the network, they're also stealing a bunch of data. So, if you wait until the first system is encrypted to stop the ransomware attack, even if you effectively stop that, gigabytes, hundreds of gigabytes, if not terabytes of your data have already been stolen, and you're going to get an email from that actor in a few days saying, hey, you haven't paid the ransom – just want you to know I've thrown your files up on this website, and I'm going to release them to everybody if you don't give me that extortion fee.
Allan Liska: [00:07:50] Which is actually an interesting trend that we're seeing. That was one that I hadn't expected, where lawyers are now getting involved in the process. So, the problem is, if you're gonna throw a company's data up on a website, you can't necessarily do it on, like, an underground forum or dark web where nobody can see it. You have to throw it up on a public website. Well, the moment you do that, you're now, you know, in sort of the realm that companies are used to operating, where the ransomware actors aren't used to operating in that realm.
Allan Liska: [00:08:26] So we saw this with the Maze ransomware, where they were one of the first to lead the extortion campaigns. They put all of the customer data up on a website hosted in Ireland, which, obviously, all of that ran afoul of GDPR. The website provider got sued by a company in Georgia whose data was exposed. And not only did the website get taken down, but the whole hosting company got shut down. So this is going to be an area where we may see more lawyers involved in this type of activity as the courts get smarter about this.
Allan Liska: [00:09:05] Another example in the UK, where a company paid a ransom and the court stepped in and demanded that the exchange actually return the ransom money. The court said it was illegal activity and the Bitcoin exchange had to actually give back some of the bitcoin that had already been taken off and laundered in other places. Which, again, this is a surprise to me – is we will see more court activity as you as the money gets – you know, as the ransom demands get higher, as the extortion demands get higher, and these operators, these ransomware operators act with more impunity, they're going to come up against, you know, not just law enforcement, but legal enforcement.
Dave Bittner: [00:09:53] Now, in terms of the ransomers getting ahold of my data – as you described, they're in my network and they're exfiltrating that data that they're then going to put on a public server somewhere – is a possible solution to that for me – or a prevention for that – that I encrypt that data on my systems so that they can't get access to it even though they're in my network?
Allan Liska: [00:10:16] Absolutely. I highly recommend that any data sitting on a desktop or a server be encrypted wherever possible. Now, where that may be a problem is if the attacker has the credentials to that machine, then they may be able to unencrypt that. So it depends on how the encryption process works. But wherever possible, if you can encrypt that data while it's at rest, it makes it that much harder for the attackers to expose that.
Dave Bittner: [00:10:55] That's Allan Liska from Recorded Future. The research we discussed was titled, "5 Ransomware Trends to Watch in 2020." We'll have a link in the show notes.
Dave Bittner: [00:11:05] Thanks to Juniper Networks for sponsoring our show. You can learn more at juniper.net/security, or connect with them on Twitter or Facebook.
Dave Bittner: [00:11:14] And thanks to Enveil for their sponsorship. You can find out how they're closing the last gap in data security at enveil.com.
Dave Bittner: [00:11:21] The CyberWire Research Saturday is proudly produced in Maryland out of the startup studios of DataTribe, where they're co-building the next generation of cybersecurity teams and technologies. Our amazing CyberWire team – working from home – is Elliott Peltzman, Puru Prakash, Stefan Vaziri, Kelsea Bond, Tim Nodar, Joe Carrigan, Carole Theriault, Ben Yelin, Nick Veliky, Gina Johnson, Bennett Moe, Chris Russell, John Petrik, Jennifer Eiben, Rick Howard, Peter Kilpe, and I'm Dave Bittner. Thanks for listening.


