Twofold snooping venture.
Dave Bittner: [00:00:03] Hello everyone, and welcome to the CyberWire's Research Saturday. I'm Dave Bittner, and this is our weekly conversation with researchers and analysts tracking down threats and vulnerabilities, solving some of the hard problems of protecting ourselves in a rapidly evolving cyberspace. Thanks for joining us.
Dave Bittner: [00:00:23] Hey, everybody, Dave here, and I want to tell you about CyberWire's new subscription program, CyberWire Pro. It's designed for security professionals and all others who want to stay abreast of cybersecurity news. CyberWire Pro is a premium service that will save you time and keep you informed. You may be saying to yourself, hey, that sounds great and something my entire organization can benefit from. We think so, too. With a CyberWire Pro Enterprise Subscription, you can make that happen. You can help to keep your organization up to date with the latest news, analysis, and trends across the evolving cybersecurity landscape. Save some money and look like a hero at the same time. We've got great discounts for government, commercial teams, and academia, too. To learn more, visit thecyberwire.com/pro, and click on the "Contact Us" link in the Enterprise box. That's thecyberwire.com/pro, and then click "Contact Us" in the Enterprise box, and we will help you become that office hero.
Dave Bittner: [00:01:25] Thanks to our sponsor, Reservoir Labs. Reservoir Labs knows that cybersecurity teams need full network visibility to discover new threats, tactics, and behaviors. This is true today more than ever. Reservoir provides solutions based on rock-solid, enterprise-class, high-speed network sensing and spectral hypergraph analytics, using advanced algorithms and mathematics to give experts an advantage. Built for critical commercial and government networks. Learn more at reservoir.com/cyberwire. That's reservoir.com/cyberwire. And we thank Reservoir Labs for sponsoring Research Saturday.
Larry Cashdollar: [00:02:09] I would really like to give them a real system to break into, and I thought the easiest way to do this would be to have a docker image.
Dave Bittner: [00:02:17] That's Larry Cashdollar. He's a Senior Security Response Engineer at Akamai Technologies. The research we're discussing today is titled, "A Brief History of a Rootable docker Image."
Larry Cashdollar: [00:02:31] I had been running some honeypot software in my malware lab that I run out of my home. And, you know, I was running pretty standard stuff like cowrie and some other honeypots that were out there. And I just – I had noticed that a lot of the attacks had been dropping off after a few weeks. And what I had suspected was that the attackers had discovered that they were in, you know, indeed attacking a honeypot, the honeypot had been fingerprinted, somehow they realized that it wasn't actually a real server or real system. And they just stopped attacking my IP addresses, and actually they stopped leaving malware on the honeypots.
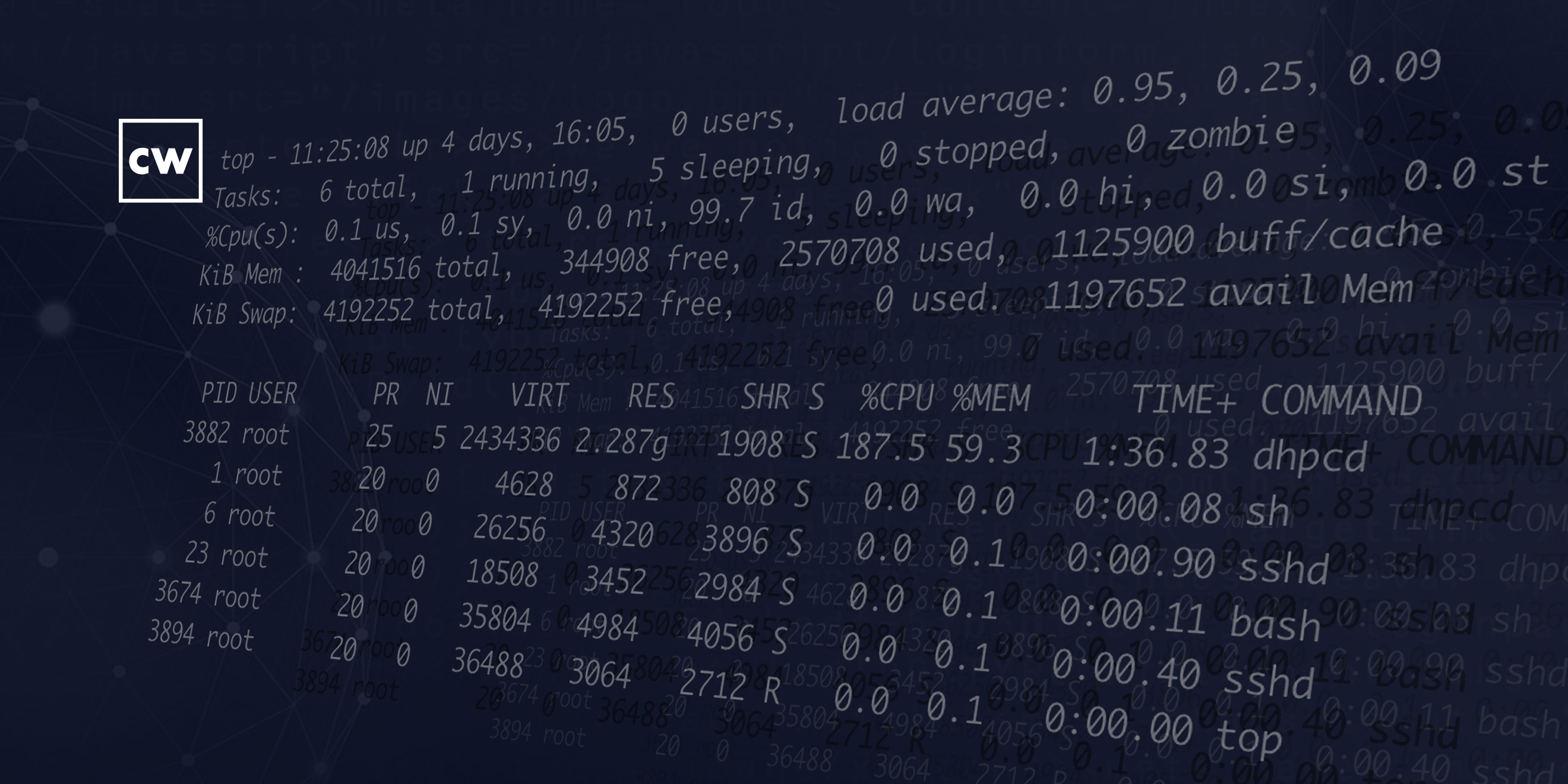
Larry Cashdollar: [00:03:18] So I thought to myself, well, I would really like to give them a real system to break into. And I thought the easiest way to do this would be to have a docker image, where I could set up a docker image on a closed-off network in my lab that would only allow SSH connections in, and then wouldn't allow any connections out, except maybe perhaps for port 80 or port 443, because I wanted these attackers to be able to download their malware, which they usually do over HTTP or FTP. And I figured through that, you know, that way I can least collect some samples. And then I thought, you know, I probably would really want to watch their actions. And I'd been interested in what sort of attacks were targeting SSH-daemon-enabled systems, or SSHd systems, that had an actual SSH server running on it. So, I decided to go back – many years ago I was a sysadmin. We had some modified SSH software, or an SSH daemon that would log all of the console connections, or all of the session information and logging information to a log file that was sent over the terminal.
Larry Cashdollar: [00:04:36] I thought to myself that I would augment that by also logging the username and passwords that were being logged into the actual system, or at least be able to document the list of credentials that the attackers were using to log into the system. So, this was a twofold snooping venture I'd gone on, where it would log the session information and also the credentials used to log into the system.
Larry Cashdollar: [00:05:03] So, I had gone and found some old C code that had been archived for years that would log session information. I had modified the SSH daemon myself to log the passwords and user names that were being logged in, and I tested it on my network myself. And once that was set up, I built the docker image that would use this SSH daemon, and then I placed it on my malware network and just set it live. And after – I'd say fifteen to twenty minutes, the machine had been picked up and there were already login attempts against it. And I think it took maybe forty-five minutes before somebody logged into it and started installing an IoT botnet binary. And then maybe a few hours after that somebody had logged in and installed a cryptominer.
Larry Cashdollar: [00:05:55] So, it didn't take long for it to get attacked. And I thought, well, I probably should take it off the network after a day, because I don't want a dozen different attackers on this docker image, all muddling up the forensics that I need to do later. So after twenty-four hours had passed, I had taken the image off and saw what sort of damage had done and then began to document everything I saw.
Dave Bittner: [00:06:20] Yeah, it's a remarkable thing that in twenty-four hours you logged this variety of attacks on this system. Can we go through them together one at a time? What did it look like?
Larry Cashdollar: [00:06:34] The first thing that I really noticed was it seemed like different groups used a different collection of known credentials. So, typically what was happening with a docker image was that the attackers were using a list of either known default passwords or logins, or ones that they had collected from other systems, and they would try and brute-force their way into the system by guessing the group password or login to the system. The usernames range between "root," to "oracle," to "mary," to "jason," to "r00t" with zeros. It was all sorts of different usernames and passwords that were wildly all over the place. Some of them look pretty complex, so they looked like they had been picked up via a previously compromised system.
Larry Cashdollar: [00:07:28] I noticed that, while the groups used different login credentials, each group would use the system for a different criminal activity. So, the first group that had logged in, they installed an IoT botnet binary on there. I think that one – I think the first one was a Mirai botnet variant, if I can remember correctly. And that one had been modified from the original Mirai botnet. You know, this one not only would scan for SSH connections and Telnet connections, but it had built-in exploits for things like ThinkPHP, and the TPLink GPON router vulnerabilities that were also compiled into this IoT botnet that first infected the docker image.
Larry Cashdollar: [00:08:14] And then shortly after that, there was an interesting piece of cryptomining malware that had been installed on the system. That one had actually added other users to the system, and it actually attempted to change the root password. I think it was – was it "haiku?" I'm trying to remember the password that they used to try and change – and that one was trying to mine, I think it was XMR, or Monero.
Dave Bittner: [00:08:44] Hmm.
Larry Cashdollar: [00:08:44] The other interesting about that one was that you could almost determine what the criminals were gonna do, depending on which login credentials they used to log in. The cryptomining malware, they were using credentials – I think root:root was one of the ones that they were using a lot to try and guess. There was oracle:oracle, root:oracle, www:www. And if the person logged in with that login credential, they would most likely use it as a cryptomining system. And, you know, if you think about the actual logins – oracle:oracle and www:www – those would be more like some sort of login you would find on a more enterprise-level system, versus, you know, a system that's an IoT device that had the default Mirai logins of root:root or root:1234567. And that system would be used for either an IoT botnet or some sort of SSH proxy, because that system was a low-level IoT system that didn't have the performance you'd use for mining crypto, whereas the one that was using the credentials that had to do with Oracle or a web server would be more likely an enterprise-level system, and that system was used for cryptomining. So you could sort of determine what the system would be used for based on the credentials they were using to try and log in with it.
Larry Cashdollar: [00:10:14] One of the other interesting things that had come up was there was a SOCKS proxy that somebody had used the SSH daemon for. They didn't use the system as a shell or do anything on the system besides relay mail through the SSH server into a Dovecot mail relay. And that turned out to be a criminal activity where it wasn't just relaying spam mail – it was relaying email that had to do with a work-from-home scam. So, you know, I noticed the mail was correspondence between multiple people using a credit card to buy high-end devices from brick-and-mortar stores. So, one was talking about buying three or four random things with a credit card at – one place was Apple Store, one place was at Best Buy, the other place was at, like, Micro Center. And they were buying things like the latest Apple Watch. And then they bought a MacBook Air and then, you know, and they did that at Apple. And then at Best Buy, they bought a Lenovo notebook. And then they went to Staples and they bought another laptop or a tablet. And then talking about sending receipts back to this other person, and then talking about, you know, using the credit card and then getting their money in return.
Larry Cashdollar: [00:11:45] And we realized that it was a work-from-home scam where somebody says, hey, you can work from home, make these purchases, and then mail me the items that you purchased and then I'll send you money through PayPal based on the purchase you bought. And then the person who actually receives the items that were mailed to them go and sell it on the underground or black market or dark web for a fraction of what they cost. They never send the person that purchased the devices any money at all, so that person ends up getting in trouble for fraud. The victim, they actually are, you know, end up getting tracked down, they're criminally charged with fraud by buying items on a stolen or fake credit card. And then the scammer who actually convinced that person to be their mule and actually go out and buy this stuff, sells it for a fraction of the price and makes an easy, you know, four, five, six dollars on an item that they bought for eight hundred because, you know, to them it's easy money. So, you know, that was something that we believed was going on. And I actually had sent what I had logged to law enforcement so that they can investigate, and, you know, sent them everything that I had collected.
Larry Cashdollar: [00:13:02] So in a lot of ways, this surprised me because I didn't expect to see mail being relayed through a proxy server that was set up through my SSH daemon, and I didn't expect to see certain clusters of user credentials that had been harvested by specific groups used for specific targeted attacks. You know, I half expected that there were large swaths of collected username and login credentials that had been stolen or, you know, pulled through SQL dumps and things like that, that the criminals sort of shared. And it seemed like each criminal entity had their own collection of credentials to use and try in a brute-force attack. So I thought that was kind of an interesting glimpse into how these groups operate.
Dave Bittner: [00:13:55] Yeah, I agree. And I wonder, was there any sense that after the initial scan happened – in other words, the folks who are looking for this open system or this available system, this connected system – after they find that it's there, was there any sense, like, an increase in activity? In other words, did they put the word out? Hey, folks, we've got a hot one here – let's start pounding on this one.
Larry Cashdollar: [00:14:23] Yeah, that's what I kind of – that's the next thing I'd like to investigate, because that's what I was wondering myself. You know, I noticed that I don't see – I'll see a little bit of traffic coming in for a specific port, and then suddenly, once that port is is open, a lot more traffic eventually starts coming in pretty quickly from other IP addresses from around the world. So, I'm not sure if groups are communicating with each other, which doesn't seem to make any sense to me, but I'm not sure how the information is distributed among teams.
Dave Bittner: [00:14:57] Yeah, because I suppose, on the other hand, they would want to keep this resource to themselves.
Larry Cashdollar: [00:15:03] Right, and that's what I don't understand – is why, after only a few minutes, does my system suddenly start to get a lot more traffic from various IP addresses. Perhaps it's one actor who is, you know, using other IP addresses to do their scanning, and those IP addresses are notified, and I'm thinking it's other actors when it might be one. But it's an interesting thing, you know, and I'm working now to try and just look at traffic showing up on my network that never actually had any business being there. Like, if I had – say I had Microsoft's – you know, a packet show up to try and connect to Microsoft's RDP server, a SYN packet. I've never had Microsoft's RDP on my network before. So I'm curious to see how long after I perhaps, you know, open that port up – how long after that do I start seeing malicious attempts against that port? So, that's something else that I'm starting to investigate in my lab.
Dave Bittner: [00:16:00] So what are your recommendations here? What can folks do to best protect themselves?
Larry Cashdollar: [00:16:05] If you were going to put an SSH daemon out on the Internet, I would recommend only allowing key – SSH/RSA key access to that system. I would disable password logins. And perhaps stick it on a different port. 22 was highly scanned for, so you might want to be more obscure – maybe put it on a different, non-standard port, like 552 or, you know, some other odd port. Even port 222 and 2222 are scanned now for SSH daemons, so those hiding spots are kind of known. And then make sure whatever service you're running on the Internet is patched regularly. Just keep an eye on that vendor and their updates to make sure that if there's a vulnerability discovered, that you're quick to patch your systems.
Dave Bittner: [00:17:02] Our thanks to Larry Cashdollar from Akamai for joining us. The research is titled, "A Brief History of a Rootable Docker Image." We'll have links in the show notes.
Dave Bittner: [00:17:12] Our thanks to Reservoir Labs for sponsoring this week's Research Saturday. Don't forget, you can learn all about them at reservoir.com/cyberwire.
Dave Bittner: [00:17:21] The CyberWire Research Saturday is proudly produced in Maryland out of the startup studios of DataTribe, where they're co-building the next generation of cybersecurity teams and technologies. Our amazing CyberWire team working from home is Elliott Peltzman, Puru Prakash, Stefan Vaziri, Kelsea Bond, Tim Nodar, Joe Carrigan, Carole Theriault, Ben Yelin, Nick Veliky, Gina Johnson, Bennett Moe, Chris Russell, John Petrik, Jennifer Eiben, Rick Howard, Peter Kilpe, and I'm Dave Bittner. Thanks for listening.


