Attackers (ab)using Google Chrome.
Dave Bittner: Hello, everyone, and welcome to the CyberWire's Research Saturday. I'm Dave Bittner, and this is our weekly conversation with researchers and analysts tracking down threats and vulnerabilities, solving some of the hard problems of protecting ourselves in a rapidly evolving cyberspace. Thanks for joining us.
Bojan Zdrnja: I was actually working on several incidents where I noticed that attackers did some, let's say, weird things with browsers.
Dave Bittner: That's Bojan Zdrnja. He's a Senior Information Security Consultant at a company called Infigo. He's also a certified instructor at the SANS Institute. The research we're discussing today is titled, "Abusing Google Chrome Extension Syncing for Data Exfiltration and C&C."
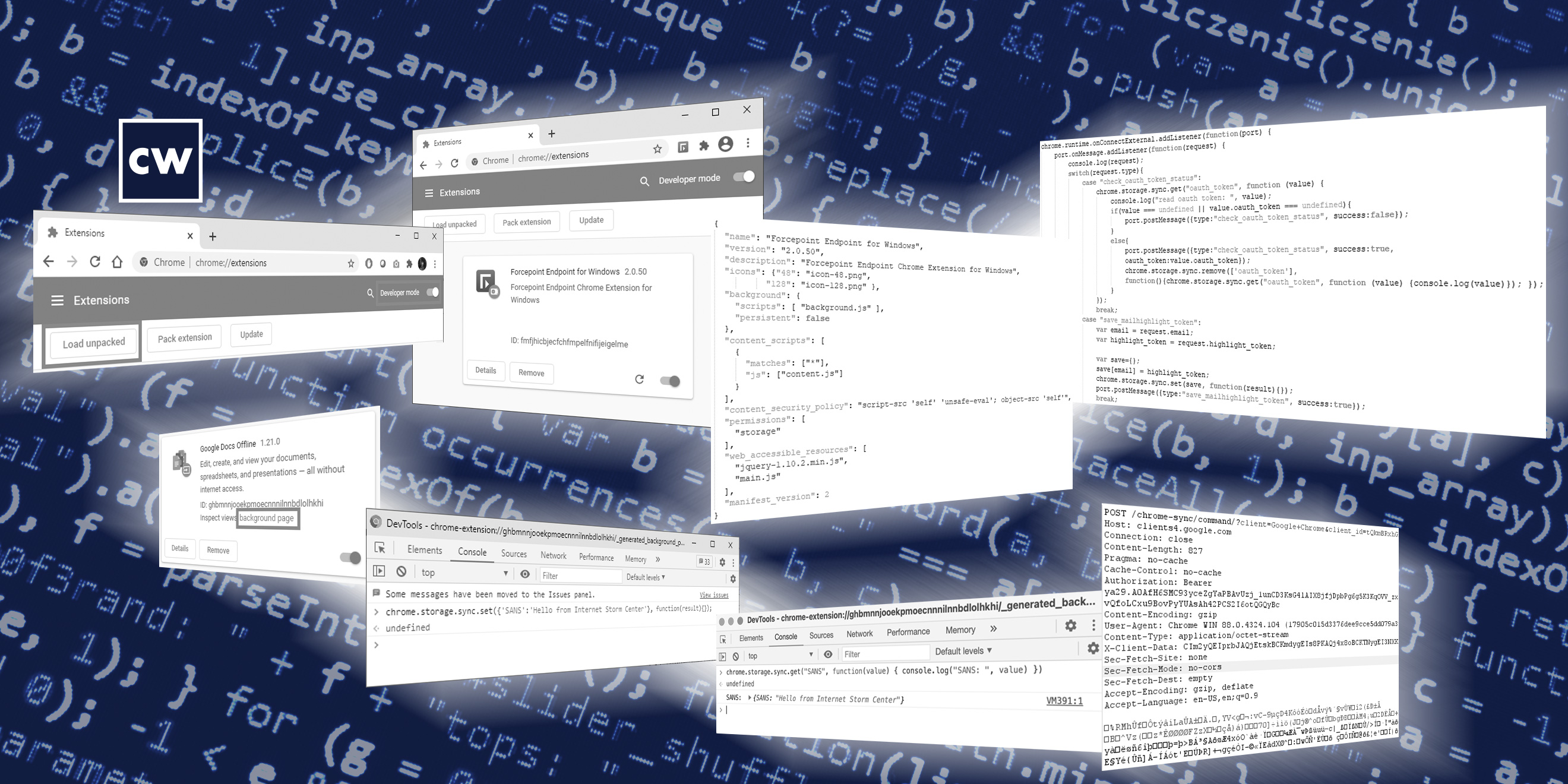
Bojan Zdrnja: So, that prompted me to do a bit more analysis of what exactly they did, and we managed to recover some files that were used by attackers, and ended up finding out something very interesting. We found out that they were using some malicious extensions which were sideloaded. So they were not available on Google's website where you normally download extensions from – they were sideloaded, they were loaded directly into Chrome. And we found out that those extensions contained some very interesting functionality that allowed them to basically abuse Google's infrastructure through a legitimate function in Chrome, which is used for syncing data between different Chrome instances. And so they were using this particular functionality as their data exfiltration and command-and-control center mechanism.
Dave Bittner: Well, let's walk through it together. First of all, a little bit of background on how Google handles extensions – what's the general functionality there?
Bojan Zdrnja: Sure. So, with extensions, we can basically add all sorts of different functionality to our browsers. And basically all popular browsers support some kind of extensions. Probably the most popular extensions are various ad blockers that quite often people actually use. They sometimes help you remove certain ads from websites, change them a little bit, so they're maybe easier to read and use. Now, those extensions are generally very, very powerful and dangerous at the same time. They are powerful because they can change basically anything you see in your browser. And for the same reason they are dangerous, because they can also modify whatever you see on a particular webpage, for example. So, there are tens, if not hundreds of thousands of different extensions. Only some of them are, of course, very popular, but there is basically nothing preventing you from producing your own extensions that it can be used in a browser.
Dave Bittner: And most people, I would say, I would hazard to guess, load their extensions through the Chrome Web Store. But as you mentioned, you can sideload them as well.
Bojan Zdrnja: Exactly. So, basically the Google Web store should be the one place to go and download your extensions from. Now, keep in mind, that doesn't need to be completely safe either. There have been malicious extensions and Google does wipe them here and there from Google Store. Actually, about a week ago, they also removed another popular extension that was found to have certain malicious elements in it. So, normally you would go to that website, download the extension, and allow the extension to run. The extension will ask you for certain permissions – a lot of people just click "OK" and allow that extension to run.
Bojan Zdrnja: Now, besides this, the Chrome web browser also allows you to do so-called sideloading, where you can load an extension directly from your hard drive. And this is basically intended to be used by developers because this will allow them to load those extensions they're working on, without going through the process of sending the extension to Google before it's ready, obviously. But as we saw, the bad guys can use that particular feature as well.
Dave Bittner: And in this case, the one you discovered, it was sideloaded. And what were they – they were pretending to be something else.
Bojan Zdrnja: Yeah, exactly. So, they sideloaded the extension, and when you create that extension, there is a file called "manifest.json" that basically defines what your extension does, what it looks like, how it will present itself to the user, and so on. So what they did was that they took the icon of another extension of a security software producer, a company called Forcepoint – which had nothing to do with the extension whatsoever – but they just took their icon from the website and they presented the add-on as a Forcepoint DLP extension for Chrome. This was obviously done in order to make it look as a legitimate add-on, where in fact it wasn't.
Dave Bittner: Do you have any idea how they were convincing people to sideload this? Do we suspect it was some sort of social engineering?
Bojan Zdrnja: Yeah, unfortunately I wasn't able to find that out. I suspect it's either social engineering, as you said, because, you know, it's not all that difficult to get people to load it, especially since it's just an extension – you can tell them, look, this is not a binary, it's just a browser extension. Or they maybe managed to compromise the machines as well and drop the file directly and just loaded them into Chrome, and after that, they don't need to do anything on that machine. They can basically use Chrome as their bot that they will control from a different place somewhere else in the world, as long as that Chrome is signed to Google to allow them to sync data of the extension.
Dave Bittner: Well, take us through what this extension actually did. What was going on under the hood here?
Bojan Zdrnja: All right, so basically what I found out and what I saw in parts that we managed to recover, was that they were able to read certain information from other websites. So basically, once you run an extension, depending on the permissions that you gave to that extension, the extension basically can see anything that's happening in your Chrome browser, or any other browser that you run with a similar extension. And that's what it is – with this extension they allowed it permission to read anything. So the extension was trying to find some authentication tokens and then relay them to the attacker by abusing the Sync feature. So that particular relay was actually flowing through Google's infrastructure. They didn't have to set up their own command-and-control center. They just relayed and synced the data through Google.
Dave Bittner: Well, let's dig into that. I mean, how does Google Sync functionality work? How is it supposed to work and how are they taking advantage of that?
Bojan Zdrnja: Sure. So it's actually a cool feature. It's a completely legitimate feature, and if any of the listeners are using Chrome, a lot of them might be using this feature already. So basically, in Chrome, when you log in to your Google account, Chrome will allow you to sync data between different Chrome instances. So, for example, if you have two laptops or if you have a laptop and your iPad or phone or anything, as long as you use Chrome on all of them and you log in to your Google account, if you allow syncing – and there is a button that you have to click on to turn on syncing – then all of these browsers will basically sync data between them. This means that they will sync bookmarks, your history of pages, but it also allows them to sync extension data.
Bojan Zdrnja: So, there is a small data storage mechanism that every single extension can use to basically store some data. That data can be stored either locally, so it's available only to this particular instance of Chrome, or it can be synced through the syncing feature between any other instance of Chrome that runs the same extension. So basically what the attackers were able to do here is to load the same extension in a different Chrome browser anywhere else in the world, login with the same account. So, they need to know the account, username and password which is logged in, signed in to Google, right? And then that other instance will simply sync data with the first instance of Chrome. And this communication works in both directions
Dave Bittner: Well, help me understand here. So, through this syncing functionality, through the browser plugin, they need to know the username, but they don't have to be logged in as that user?
Bojan Zdrnja: OK, so they need to login in Chrome as the user that is used to seeing the data. So, in the particular incident I was investigating, the legitimate user actually didn't use that feature at all. So what the attacker did was that the attacker signed in on behalf of that user with a throwaway account on Google and then used that account to sync data.
Dave Bittner: I see. Now, there's some functionality going on behind the scenes here where extensions are able to swap information between them. What's going on there?
Bojan Zdrnja: Yeah, exactly. So, Google actually provides extension developers with a legitimate mechanism to perform that, because they expect that extensions will need to sync some data. So, for example, if you have one Google Chrome instance and you change something in an extension, you change a setting, then as a user, you would probably expect that the same setting is changed in your other instance of Chrome, for example, on your other laptop. So that's why they added this feature for extensions. And as I said, it's a legitimate feature which makes sense. Now, the malicious extension basically abuses this particular feature, and it has a mechanism that allows it to set keys with certain values, and those keys with values will be very, very quickly synced between those two instances by using Google's infrastructure.
Dave Bittner: In a matter of seconds, right?
Bojan Zdrnja: Exactly, in a matter of seconds. Now, you can't transfer gigabytes, really. There is a limit that Google imposes here. It's in the original text, but generally, from some of the tests I did, it will allow you to exfiltrated a couple of megabytes per hour, which, in a real-world scenario, would be probably good enough for an attacker that wants to find a very stealthy way to exfiltrate data from an environment, especially since this data will be flowing only through Google. And if you are doing some network inspection, you will not see absolutely any suspicious traffic apart from traffic going to Google's website.
Dave Bittner: Right, and one of the things you point out in your research here is that makes it hard to block this, because you would affect legitimate, good functionality from Google if you did.
Bojan Zdrnja: Exactly. Exactly. So, the website that's being used by the syncing feature is "clients4.google.com," and the same website is actually used by Chrome, for example, when you started, to figure out if you are connected to the Internet or not, if you have some blockers on your network, or similar. So if you just say that you don't want to allow anyone in your enterprise to access this website, you might break some legitimate functionality of Chrome. So it's not that easy to disable the syncing feature.
Dave Bittner: So, what options do the folks have to protect themselves against this?
Bojan Zdrnja: So, that's a great question, and luckily there is a way to make this secure in enterprise environments primarily. So, first of all, with any extension, as we already mentioned earlier, since they can be malicious, we should be very careful when loading those extensions. Now, there is nothing to prevent people from sideloading extensions if they want to. But luckily for us, Google did publish policies that can be used, for example, in Windows Domain, as a group policy that your enterprise administrator can push and either completely disable extensions or just create a whitelist of extensions that you want to allow your users to use, and then blacklist absolutely everything else. And that's something that I would definitely suggest that any enterprise does, because it will make your Chrome installations across your enterprise much more secure. It will give you power of controlling which extensions are installed and which are not, so basically, you can block whole classes of attacks with that.
Bojan Zdrnja: Do you have any idea who's behind this? Anything in terms of attribution or who they're targeting?
Bojan Zdrnja: Not at this moment, unfortunately. This was found as a couple of incidents in which – and it was not related to those incidents. So the attackers probably dropped the file by accident, because they used some other functionality that we found. So at this point in time, I don't know what exactly they were trying to steal or who is behind this.
Dave Bittner: Yeah. It's certainly a clever attack. And it's one of those ones that I think leaves you both impressed and scratching your head. You know, it's pretty straightforward, but, boy, it seems to be effective.
Bojan Zdrnja: Yeah, exactly. Exactly. There is the beauty behind this is that, as you said, it's pretty straightforward. It's actually relatively simple, and you don't need to be the world's best developer to code this. But at the same time, it is very, very stealthy and it definitely makes me feel unpleasant about all those extensions that I use as a user as well, because I like some functionality they provide.
Dave Bittner: Our thanks to Bojan Zdrnja for joining us. The research is titled, "Abusing Google Chrome Extension Syncing for Data Exfiltration and C&C." We'll have a link in the show notes.
Dave Bittner: The CyberWire Research Saturday is proudly produced in Maryland out of the startup studios of DataTribe, where they're co-building the next generation of cybersecurity teams and technologies. Our amazing CyberWire team is Elliott Peltzman, Puru Prakash, Stefan Vaziri, Kelsea Bond, Tim Nodar, Joe Carrigan, Carole Theriault, Ben Yelin, Nick Veliky, Gina Johnson, Bennett Moe, Chris Russell, John Petrik, Jennifer Eiben, Rick Howard, Peter Kilpe, and I'm Dave Bittner. Thanks for listening.


