Diving deep into North Korea's APT37 tool kit.
Dave Bittner: Hello, everyone, and welcome to the CyberWire's Research Saturday. I'm Dave Bittner, and this is our weekly conversation with researchers and analysts tracking down threats and vulnerabilities, solving some of the hard problems of protecting ourselves in a rapidly evolving cyberspace. Thanks for joining us.
Hossein Jazi: We do the triage, looking at the sample, and if it does something anomalous, we take the sample for further investigation. This is one of the samples that caught our interest.
Dave Bittner: That's Hossein Jazi. He's a senior threat intelligence analyst at Malwarebytes. The research we're discussing today is titled, "Retrohunting APT37: North Korean APT used VBA self decode technique to inject RokRat."
Hossein Jazi: I took the sample and decided to do a further analysis, and then figured out, OK, this is something interesting related to an APT, and that was the time that I started to look for more analysis and preparing a blog on that.
Dave Bittner: And is your sense that this is a particularly targeted campaign, that they're going after specific individuals here?
Hossein Jazi: Yeah, we believe this attack was – the target of this attack was the government of South Korea, and it's really aligned with the interests of this state-sponsored APT that is targeting the government of South Korea.
Dave Bittner: Well, let's go through it together. I mean, there are a lot of steps here and some really interesting technical things that you all have discovered here, why don't we walk it through step-by-step? I mean, if I'm the target of these folks, how are they typically going to start their interaction with me?
Hossein Jazi: OK, so I would like to a little bit speak about this APT and then go through this attack.
Dave Bittner: OK.
Hossein Jazi: So, APT37 is one of the most sophisticated North Korean threat actors that has been active since at least 2012. This group, also known as ScarCruft, Group123, Reaper, or Geumseong121. This group has mainly targeted South Korea, like the attack we analyzed, the target was South Korea. But this group also has targeted several other countries, such as Vietnam, Japan, China, some countries in the Middle East.
Hossein Jazi: So, the main initial infection vector used by this actor is mainly spearphishing emails. But they also use some other techniques, such as a strategic web compromise in which they compromise a website to host their malware or host the malicious document.
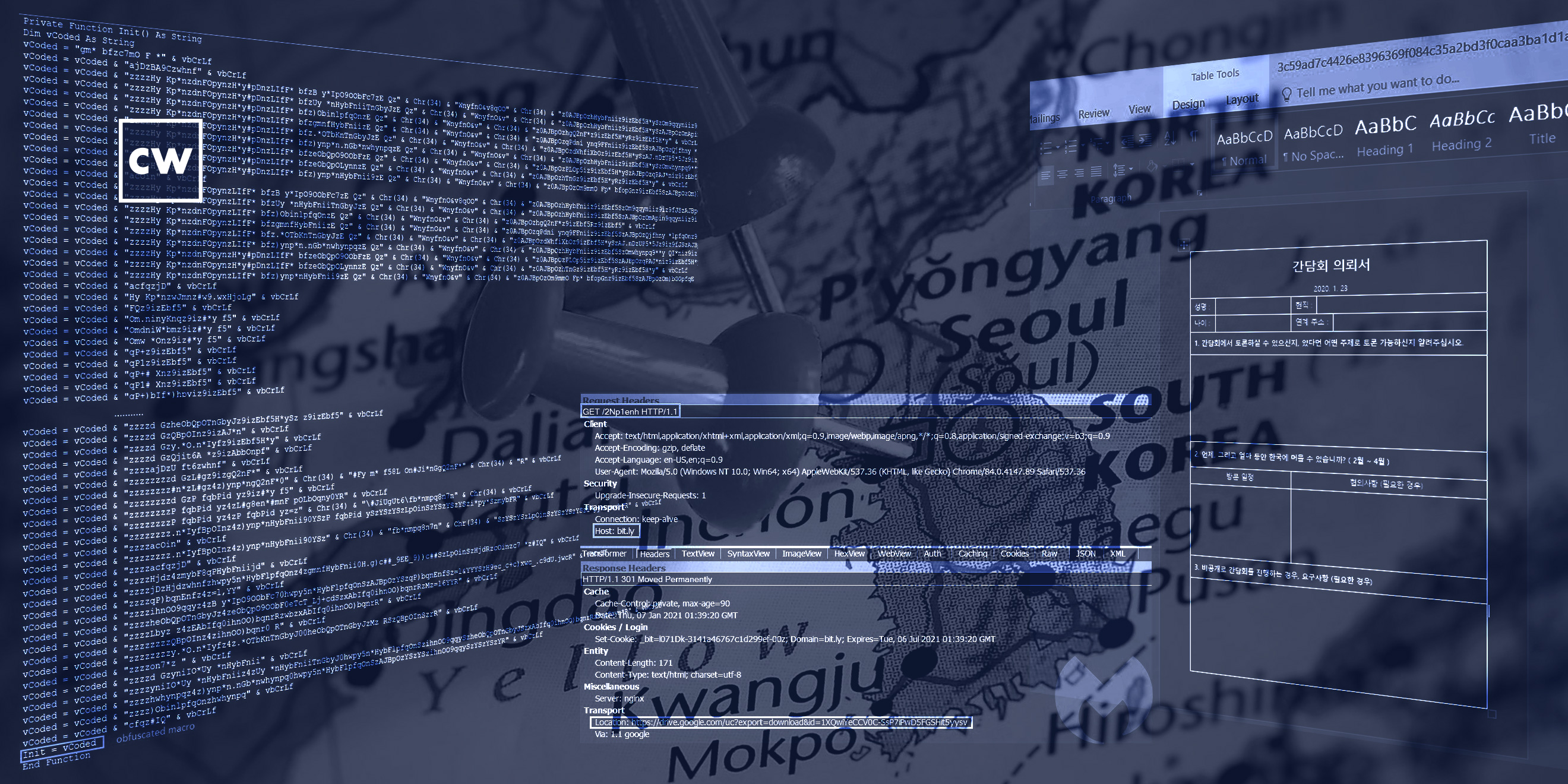
Hossein Jazi: So, the one we analyzed, we believe it started with a spearphishing attack. So, they sent an email to a victim, and they might attach a malicious document directly to the email, but this actor has used the links to host the malicious document in Google Drive in the past. So, since we didn't have access to the phishing email, I cannot say which one, but possibly they used one of these techniques to send the email. So that, as I said, it started by sending a phishing email which has a document attachment or has a link that redirects the victim to download the document. And usually this group may only use a Hangul document, which is a popular word processor in South Korea. But this one was interesting one, and they use Microsoft Office to start their attack. This is not the first time that they use this Microsoft Office, but this is not the common one.
Dave Bittner: Yeah, well, I mean, let's continue down that path. So I get hit with this spearphishing email and I take the bait and I click on the link. What happens next?
Hossein Jazi: So, yeah, so if we assume that the phishing email contains a malicious document, then the victim clicks the document and opens the document and the document asks you to enable content. So when you enable the content, the macro is executed in the background and performs some malicious activity, which in this case it injected a payload into Notepad. But what was interesting is the techniques that's used in the malicious macro. So, the technique, we call that "VBA self decode."
Dave Bittner: Yeah. So let's go through that together. As you mentioned, this self-decoding technique is is fascinating because you've got VBA macros inside of VBA Macros. Take us through this step-by-step.
Hossein Jazi: Yeah, sure. So, VBA self-decoding is a technique in which a malicious macro is embedded within another macro and then is executed dynamically without being written into the disk. So, in other words, we can consider this one as an implementation of packer technology within Microsoft Office. So, here there is an unpacker stub which is a macro that unpacks or decodes the malicious macro and writes it into memory space of the Microsoft Office, and then jumps to the start of the new macro and executes it.
Dave Bittner: And so by doing this, it helps obfuscate what's going on here, but as you mentioned, it also keeps it from being written to disk, which I suppose would be a way that anti-malware would be able to pick up on it.
Hossein Jazi: Yeah, exactly. Because what you see – you see the unpacker stub, or a macro that unpacks the malicious macro, so you want to see the real macro that is being executed, and you want to see what's going to happen when the macro's executed. You just see the macro that's doing some malicious activity, but you never know what was going to happen.
Dave Bittner: So this macro within a macro gets executed, and then what happens next?
Hossein Jazi: OK, so first of all, to execute the macro dynamically within the macro, the VB object model needs to be bypassed, because Microsoft Office, by default, disables the dynamic execution of macro. So, before decoding the macro, this malicious document bypassed the VB object model by modifying its registry key. After that, it does the process of decoding, and in the process of decoding, they have a custom decoder that decodes the macro. So when they decode the macro, they create a module within the space of Microsoft Office and jump to the start of the new macro. This is where the main malicious behavior is happening. So, here there is a shellcode that will be injected into Notepad.
Hossein Jazi: So they create a process which is a target process, and it's Notepad here, and then create a memory space within Notepad, and then inject the shellcode into that memory by calling WriteProcessMemory, and then execute that shellcode within the Notepad process by calling resume thread.
Hossein Jazi: So what this shellcode does is going to Bit.ly that redirect the machine to a Google Drive to download the final payload, which is a variant of RokRat. So this is, like, clever techniques used by this attacker that used the URL shortener to hide the URL that they are contacting, and then hosted their payload into Google Drive. So it looks legitimate and nothing malicious, and the payload hosted in Google Drive is encrypted, so it won't be flagged by Google to be malicious. So then they take the shellcode, take their payload, decrypt that payload and execute it.
Dave Bittner: Hmm. And so what is the functionality, there, of RokRat?
Hossein Jazi: So, RokRat is a cloud-based RAT that had first, I think, used by this APT around 2017. But the main functionality of this RAT is to steal information from the victim. So, it has the capability to take screenshots of the victim. It has capability to record audio. It has capability to steal credentials from the browser, and then send those collected info to cloud services, such as Pcloud, Yandex, Box, Dropbox. So, this is another clever technique used by RokRat to communicate, to perform C&C communication through cloud services. So still they are trying to hide or pretend that their command-and-control communication is legit.
Dave Bittner: Hmm. Now, the system itself, I mean, as it's going through this process, it's checking to see if it's running, for example, in a sandbox or something like that, and it's trying to hide itself.
Hossein Jazi: Yeah. So, you know, most of the APTs trying to detect antianalysis or check if they are running in a sandbox environment. So this is the same. So they are doing some basic checks, such as looking if they are running in the debugger by using the API, like IsDebuggerPresent or GetTickCount, or also check for VMware-specific files, or looking for different DLLs. And if they found those artifacts, they won't show the behavior.
Dave Bittner: So how successful is this system, you know, going through the various steps here, how successful is it at evading detection?
Hossein Jazi: I think this would be a really successful for several reasons. First of all, they have started the attack by VBA self-decoding technique. So I assume that with the carefully crafted the document to convince the victim to click to enable the content, which is the main step, then they can be like – perform behavior like in accord – like, structure. So you cannot – it would be really hard for a defender to figure out if this is a legit or malicious behavior because it spawns Notepad and then injects payload within Notepad, and the C2 communications are going to cloud services, which looks legit, and also the payload downloaded from the Google Drive. So, all looks legit and pretends to be legitimate communications. So I think it would be a successful attack.
Dave Bittner: Well, what are your recommendations, then, for folks to best protect themselves?
Hossein Jazi: So, this technique can easily bypass static and signature-based detection. So, the recommendation would be monitor dynamic behavior of Microsoft Office. So in that way, you will figure out, oh, there is something happening in this machine because Microsoft Office has spawned Notepad, which is not something normal, and then Notepad is doing some communication, it's sending some files from my machine into a cloud service. I know I'm using, for example, Box, but why are there some files transferring to Box from my machine to a Box that I don't know. So I think dynamic analysis would help figure out or defeat this attack.
Dave Bittner: Our thanks to Hossein Jazi from Malwarebytes for joining us. The research is titled, "Retrohunting APT37: North Korean APT used VBA self decode technique to inject RokRat." We'll have a link in the show notes.
Dave Bittner: The CyberWire Research Saturday is proudly produced in Maryland out of the startup studios of DataTribe, where they're co-building the next generation of cybersecurity teams and technologies. Our amazing CyberWire team is Elliott Peltzman, Puru Prakash, Kelsea Bond, Tim Nodar, Joe Carrigan, Carole Theriault, Ben Yelin, Nick Veliky, Gina Johnson, Bennett Moe, Chris Russell, John Petrik, Jennifer Eiben, Rick Howard, Peter Kilpe, and I'm Dave Bittner. Thanks for listening.


