Leveraging COVID-19 themes for malicious purposes.
Dave Bittner: Hello everyone, and welcome to the CyberWire Research Saturday. I'm Dave Bittner, and this is our weekly conversation with researchers and analysts tracking down threats and vulnerabilities, solving some of the hard problems of protecting ourselves in a rapidly evolving cyberspace. Thanks for joining us.
Joe Slowik: Just in the course of every day, keeping an eye on the security landscape, looking for things that just seem interesting and related to items of interest, and, you know, the main item of interest for everyone right now is still and remains the ongoing pandemic...
Dave Bittner: That's Joe Slowik. He's a Senior Security Researcher at DomainTools. The research we're discussing today is titled, "COVID-19 Phishing With a Side of Cobalt Strike."
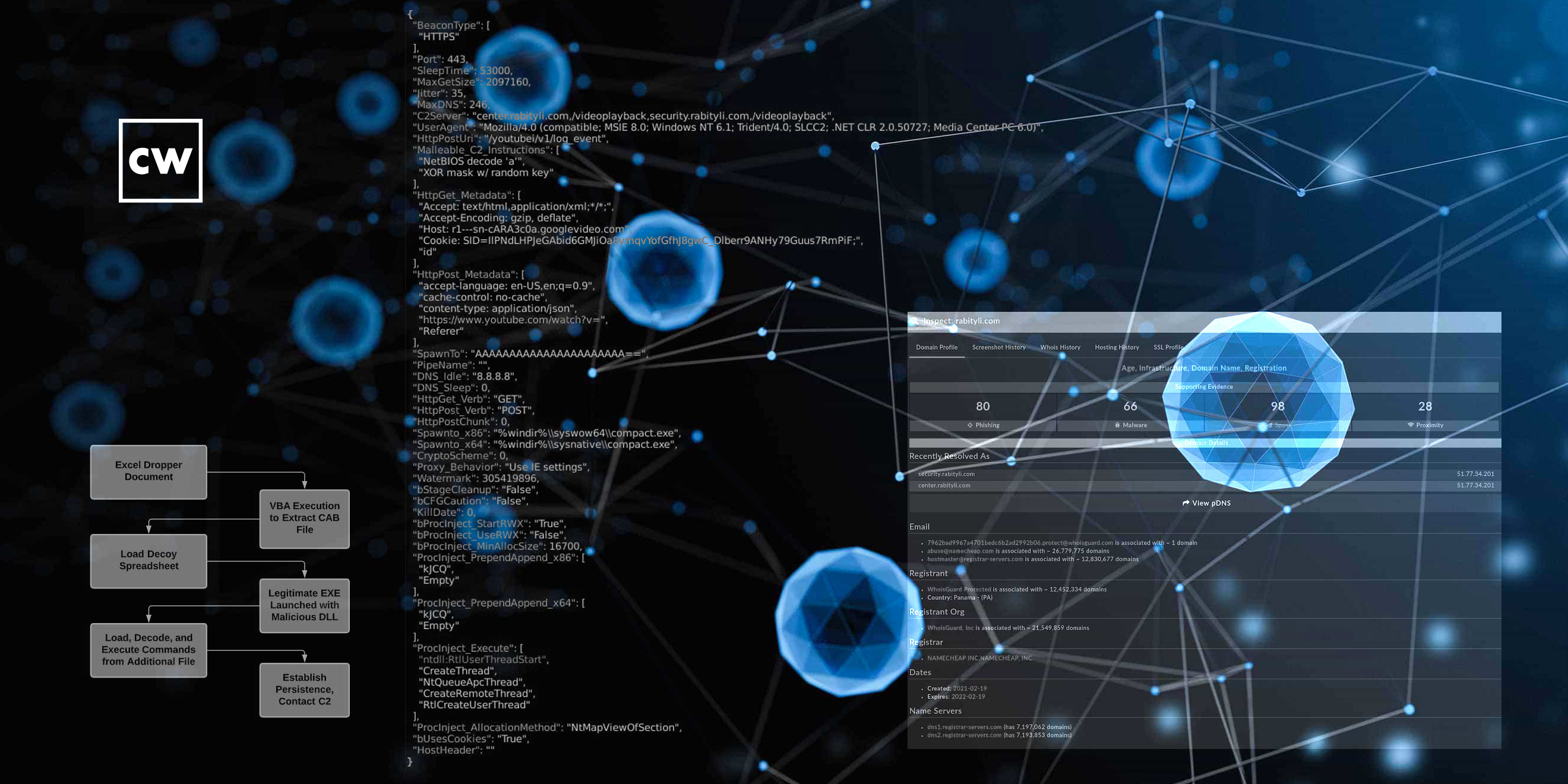
Joe Slowik: ...And related to that, we identified in the wild, a Microsoft Office spreadsheet Excel file that had a COVID-19 theme related to vaccines. So, this is interesting, and had some curious scripting items associated with it, or Visual Basic for Applications macros within the document. And so, interest was piqued a little bit, and that led to an investigation that really, you know, as these things kinda do, went down a little bit of a rabbit hole. Because while this wasn't – you know, it's always troubling to use words like "complex" or "sophisticated," because those are kind of weasel words and this isn't any of those things, but that almost stands out on its own for a sort of brute-force simplicity that really what we were looking at here was a Excel file that contained an encoded object that turned out to be a Windows Cabinet file that then had some bonus materials inside of it. And that's where things start to get really interesting.
Dave Bittner: Well, let's walk through it together here. I guess it's worth mentioning, as you do in your research, that if you are running a current version of Excel, that you're already sort of protected against this.
Joe Slowik: Yes, that's right. This was really designed to run in legacy Office environments, which can tell us a few things already, since this is a recent document – all items related to it show that it was created within the last month or so. But the most recent Office versions, let alone updates of those versions, will prevent this from running. So this implies that the adversary in question is fairly confident that its intended audience is using older versions or perhaps even pirated versions of the software. So that can start focusing our efforts on, you know, this is probably not targeting the latest and greatest or the most up-to-date organizations, but rather something else. What that something else is is certainly up for discussion, but it does look weird, if nothing else.
Dave Bittner: Yeah. Well, you know, let's say I'm minding my own business here and I come across this file that promises to show me a list of the various COVID-19 vaccines, and I think that's something that I may be interested in. I open up this document – what starts happening behind the scenes?
Joe Slowik: So, if you're running a older version of Office, what will happen is you'll get the classic, "Would you like to open this document and disable protected mode?" And then with some macro enablement later in order to show the actual content, behind the scenes, this will launch a sequence of actions that uses built-in system functionality to then construct a sequence of commands that will, as so many adversaries do, launch some PowerShell as well as some other scripting items in order to decode and then execute a binary file. But what's interesting about this binary file is that it's actually a legitimate executable that's used, and an older one to boot – which kind of hints back to, you know, some legacy components being used in this infection chain – but leveraging a technique of trying to get malicious code to run under a code-signed front or code-signed basis.
Dave Bittner: Yeah.
Joe Slowik: So, the way this works in this specific instance is the attackers took a legitimate F-Secure binary and used the legitimate executable, but then used a modified dynamic link library associated with it and took advantage of something called DLL path hijacking in order to load the malicious content from the DLL under the signed executable. And this is a method used by a number of attackers in order to gain greater trust and evade defenses when trying to gain malicious code execution.
Dave Bittner: Mm-hmm. Can you explain it to us? It's fascinating here – can you walk us through how it works?
Joe Slowik: Sure. So, the way that this works is that for the majority of programs operating in Windows environment, that when they're associated with a dynamic link library, or DLL file, they will typically search for that library by first checking for the same folder that the executable ran in, and then apply a search algorithm of either moving up the file system or checking certain locations, like in the System folder, for where that DLL is anticipated to be located. Well, an attacker can take advantage of this by running the legitimate executable in a non-standard location or a custom location, such as just a folder created in a temporary location around the desktop and dropping a version of the DLL with the same name in the same directory to take advantage of that sequence of that search sequence. And that could be used to run the content of the DLL file under the context of the legitimate signed executable.
Dave Bittner: Wow. So, the system goes and checks the signing of the executable, says "all is good here," and then basically gets tricked into running something that has the same name – is that basically how it works?
Joe Slowik: Basically, yes. And like I said, this is a way of circumventing certain types of application control by really taking advantage of a feature, really. You can't really call this a bug because it's intentional by design as a way of facilitating program execution.
Dave Bittner: It was interesting, sort of as a side note in your research, you mention that folks have been using this file from F-Secure for quite a while now. I mean, is there a subtext there? Is it just convenient?
Joe Slowik: Right. And, you know, that was something that was really curious about this entire sequence of events, is that we see a blending of fairly old and previously disclosed techniques down to specific versions and types of payloads like the F-Secure binary used in order to launch this incident, and then blending in newer items, like ultimately leading to a Cobalt Strike beacon payload, which we can get into a little bit later. And it is very strange because, you know, you could look at this from a number of ways, and this maybe ties into the targeting of legacy versions of Microsoft Office, that the intruder in this question having some background or understanding about the environment that they were targeting, knew that they didn't need the latest and greatest in order to get into this environment, that they were operating with legacy systems or not the most up-to-date security, as well as just basic operational tools. And so they could recycle well-known, previously disclosed events. And there is a certain economy or efficiency that gets associated with this activity that, you know, you don't risk burning or disclosing novel techniques and other items in this way while still achieving mission success or effectiveness.
Dave Bittner: Right, right. That's interesting. Well, let's walk through what happens next. I mean, they're able to execute their file here. Where do we go from here?
Joe Slowik: Right. So, after the file is executed, there is a sequence of events that then, you know, a decoy spreadsheet is loaded, which provides a list of COVID-19 vaccines listed in what is presented as order of safe to the least safe, which is interesting if you look at the content itself, we can discuss that if you'd like. But then we have the DLL loaded into memory, and then this loads and decodes a third file that's also included with the Cabinet file that contains obfuscated commands that begins establishing persistence and contacting a command-and-control domain. So really, we're getting into the sort of meat of the activity here, which, with further analysis and being able to capture the network traffic in question shows that we have an adversary going to, you know, again, a fairly tried-and-true method, but one that's a bit more recent than some of the other things we've discussed so far, in using a Cobalt Strike beacon payload – in this case, using some masquerading of tunneling the actual command-and-control underneath a lookup to Google Video or YouTube services to add a further layer of obfuscation and defense evasion to matters.
Dave Bittner: Wow. And this is presumably effective. I mean, this they're successful in having this fly under the radar.
Joe Slowik: Right. So, that's another interesting thing about this, is that unless you are performing SSL or TLS capture and inspection within your network environment, the communication, it will look to anyone observing that you are initiating communication with YouTube or Google video, which maybe is a little odd, depending on where the communication is coming from or seeing it initiated from Excel or from another unfamiliar process. But still, you're probably not doing that level of logging if you're already running very legacy versions of Office and whatnot. And so that really serves to hide that you ultimately have communication going to a adversary-created and controlled domain – "rabityli" – I don't know really how to pronounce it, if it's even a real word. It's probably more of a made-up item. So, yeah, I mean, it just adds another way of trying to avoid attention and response.
Joe Slowik: And so that's where this campaign gets kind of curious, is that we have that combination of recycled legacy, fairly old tradecraft in some instances that look like it's recycling things that were first observed in 2014, with fairly recent and more technically savvy items such as, you know, just using the digital search order hijacking method to execute with code-signing privileges and using this way of circumventing network traffic monitoring and analysis, unless you're doing SSL inspection, to obfuscate what the ultimate C2 location would be. So, yeah, it's, again, a very interesting combination of techniques as part of this intrusion operation.
Dave Bittner: Yeah, it's almost like these folks are reaching into their bag full of Lego bricks and, you know, those old bricks work just as well as the new ones. They all click together, right?
Joe Slowik: Right. And I think that's almost a really good observation about network intrusion activity more generally is that I think we've kind of built this expectation that adversaries, especially if we're talking about state-directed adversaries – which this might be, we don't quite know, there's some possibilities here if we can get into – but anyway, that such adversaries will use custom bespoke, purpose-built tooling for their campaigns. When really, what we've observed over the last couple of years especially, is adversaries are very happy to use whatever works. And if that means using some scripts and tools procured via GitHub, a cracked version of Cobalt Strike, or recycling tradecraft that was documented on a publicly accessible blog from over five years ago, that's fine. Because I think what we're starting to see is adversaries realizing that they don't need to invest a inordinate amount of resources in tooling if they can just identify what's good enough for the environments they think that they'll be operating within.
Dave Bittner: Now, as part of your research, you and your colleagues went looking for some more samples of this, and you did find some similar documents.
Joe Slowik: We did. And, you know, looking at other documents, both by the structure of the Excel files themselves, as well as looking at where these documents may have come from – which looks like a hosting provider or hosting service located in Vietnam – we found several other documents with health-related themes where the title or file names of the documents were in Vietnamese, as well as the content of the spreadsheets themselves, including things like a list of cancer centers and other items. And so, expanding out from that original list of COVID-19 vaccines and seeing this further landscape, it starts looking like there's a general theme here from December through March of targeting Vietnamese-related entities that were operating in the healthcare space, which was very interesting when, with a little bit of tried-and-true web searching, we were able to identify a couple of government communications that had been uploaded to the Internet or were accessible over the Internet from provincial authorities in Vietnam, warning about this sort of phishing activity in January of this year, which seems to lend some support to the idea that this is something that, if not exclusively targeting Vietnam, at least had a focus on Vietnamese institutions.
Dave Bittner: Well, and that leads us to the possibility that this could be the work of a threat group called Goblin Panda? What do we know about them?
Joe Slowik: Right. And this was really interesting because, you know, this is one of those cases where we see some things that seem more than just a coincidence, whereas other items that are more difficult to try to really make this connection. So, Goblin Panda, which, you know, since we're using the CrowdStrike naming convention here, is a entity that is assessed or thought to be linked to Chinese interests in some fashion, although it's never been conclusively proven, has previously used some of the techniques that we identified in these documents, such as the search order hijacking for DLLs, targeting of Vietnam, as well as another sort of oddity of using older vulnerabilities, execution pathways and Office formats as part of their activity in targeting entities like the government of Vietnam. So, while we could look at this as a series of coincidences, the fact that there was more than one here certainly indicates that this is something worth considering, even if we can't prove it just yet. But it's also worth noting that these are techniques that are generally available to a number of threat actors.
Joe Slowik: Another consideration is that Goblin Panda is not previously linked to deployment of Cobalt Strike, usually associated with tools like PlugX or Chinoxy variants and similar, and use of a Cobalt Strike beacon payload would be something new. So, again, there's items that seem to relate to this entity, including targeting and geographic emphasis, and then other items which are a little more indeterminate, at least without having additional data.
Dave Bittner: Well, I mean, let's go through some of the take-homes together. And why don't we start here by, you know, what opportunities would folks have to protect themselves against this along the various steps of the way?
Joe Slowik: Right. I mean, first and foremost, we have just run up-to-date, patched software.
Dave Bittner: Right.
Joe Slowik: That might seem like a silly, stupid one, but, you know, it still comes into play and goes into the overall concept of reducing attack surface. After that, you know, we have options such as identifying interesting process change or process execution chains such as the classic identifying scripting frameworks being executed from Office documents. So, seeing PowerShell or wscript or similar items with a parent process of Microsoft Office is an almost universal sign that something suspicious, if not outright malicious, is going on.
Joe Slowik: And then another interesting item, as we start getting into some of the more operationally secure or security-savvy elements of this campaign. So, for example, the DLL search order hijacking, you know, this might seem a difficult problem, but, you know, in well-architected environments, we can do things like search for or even outright prevent the execution of binaries in untrusted locations like user temporary directories or similar items. I mean, obviously, there is some pain that could be associated with that in terms of convenience, but either detecting or outright preventing such activity can drastically reduce scope if the environment is set up to allow for such activity to take place.
Joe Slowik: Similarly for the network communication aspect, and I think this is something that we're increasingly seeing with a number of items, you know, adversaries are aware of the limitations imposed by the increasing adoption of encrypted communications, whether we're talking about HTTPS or DNS over HTTPS, or, you know, similar widespread adoption of SSL encryption. As a result, more organizations will need to ask the question, is it appropriate to begin proxying and capturing encrypted communication for defensive purposes? There's obviously a number of potential risks and drawbacks involved in doing so, but, you know, as we see, adversaries just rely upon legitimate encrypted communications channels to mask or hide their operations, it's something that organizations are going to need to think about, because for certain techniques, such as what we talked about here, it becomes one of the only ways of really detecting this sort of activity with any degree of certainty.
Dave Bittner: Our thanks to Joe Slowik from DomainTools for joining us. The research is titled, "COVID-19 Phishing With a Side of Cobalt Strike." We'll have a link in the show notes.
Dave Bittner: The CyberWire Research Saturday is proudly produced in Maryland out of the startup studios of DataTribe, where they're co-building the next generation of cybersecurity teams and technologies. Our amazing CyberWire team is Elliott Peltzman, Puru Prakash, Kelsea Bond, Tim Nodar, Joe Carrigan, Carole Theriault, Ben Yelin, Nick Veliky, Gina Johnson, Bennett Moe, Chris Russell, John Petrik, Jennifer Eiben, Rick Howard, Peter Kilpe, and I'm Dave Bittner. Thanks for listening.


