Primitive Bear spearphishes for Ukrainian entities.
Dave Bittner: Hello everyone, and welcome to the CyberWire's Research Saturday. I'm Dave Bittner, and this is our weekly conversation with researchers and analysts tracking down threats and vulnerabilities, solving some of the hard problems of protecting ourselves in a rapidly evolving cyberspace. Thanks for joining us.
Gage Mele: Primitive Bear is an interesting group in that they primarily focus on Ukrainian entities and individuals, so you see a lot of their malicious documents are themed around these government entities.
Dave Bittner: Our guests this week are Gage Mele and Yury Polozov. They are both members of Anomali's Threat Research Team. The research we're discussing is titled, "Primitive Bear (Gamaredon) Targets Ukraine with Timely Themes."
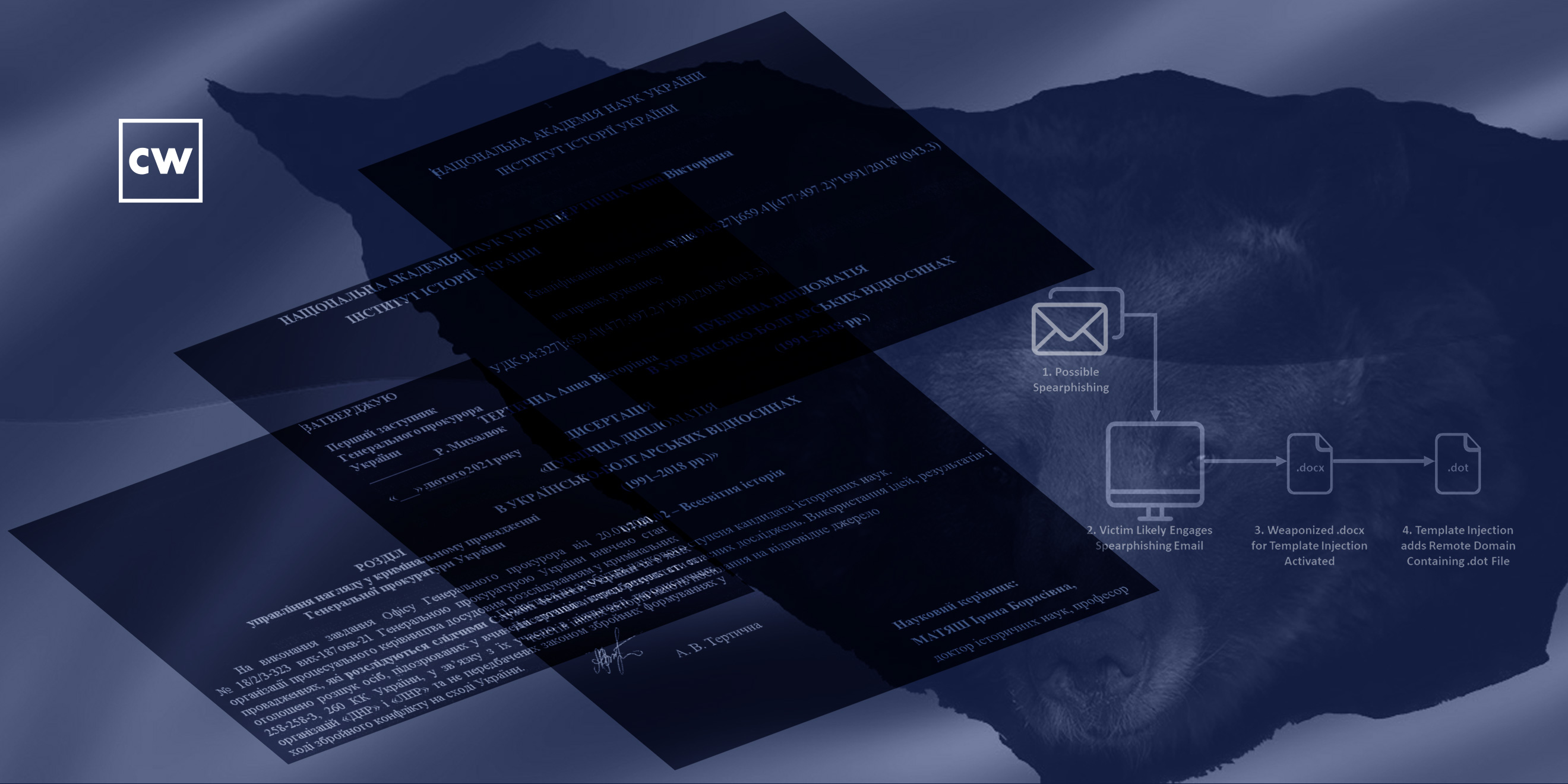
Gage Mele: And they like to use template injection...
Dave Bittner: That's Gage Mele.
Gage Mele: ...So typically they'll have a .docx file that'll reach out to a domain to download a template. And then, unfortunately, in this case, the template domains were down, so we don't know what the .dot files exactly were doing. In previous activity, these .dot files contained a VB script, and then these VB scripts would begin the infection chain. But unfortunately, in this case, we're not sure. But we wanted to show that they're still using these TTPs, and in this case, in quite a timely manner as well.
Dave Bittner: And Primitive Bear, we are confident in saying is a Russian group.
Yury Polozov: Yes, absolutely...
Dave Bittner: That's Yuri Polozov.
Yury Polozov: ...Some open-source reporting even connects them directly to Russia's Federal Security Service, or FSB. So it was some irony to see some of the decoy documents that we show in this paper actually referring to FSB as a topic.
Dave Bittner: Well, let's walk through it together. I mean, let's go through step-by-step. If someone were found themselves in the target of this group, what would happen? Can you take us through it?
Gage Mele: So, yeah, they operate typically through spearphishing. There's likely other ways they accomplish their objectives, but usually they'll do spearphishing. So, something that looks legitimate to someone. And in this case, it was timely to current events that were taking place in Ukraine and Russia with the military buildup at that time. So they'll use things specific to that timeframe to appear more authentic. And then as soon as you click and open that file, it tries to download that remote template. And if that succeeds, potentially bad news for you.
Dave Bittner: So, at that point, it would try to get a second-stage payload, that would be the actual malware itself, we suspect?
Gage Mele: Correct. That .dot file is where the bad stuff lives.
Dave Bittner: I see. And in this case, as you say, the servers to deliver that were not up and running, so the exploration sort of ended there.
Gage Mele: Unfortunately, yes. These groups are smart in that case, where they'll have some dedicated infrastructure. They'll turn it on, launch a campaign, turn it off.
Yury Polozov: Yeah, and the same about the decoy documents. They're very sophisticated, all the research that we did showed that the data, like sensitive contact information in those decoy documents, are very accurate. For example, some of them were referring to Ukrainian embassies in different countries or some military exercises and related to it. And it was always timed, often the timestamp in the document was very close, typically the same months that actually attack happened.
Yury Polozov: And one document in particular, it was some decoy, it was some scientific paper about Ukrainian public relationships with different countries. And so the researchers saw this decoy used in attack, and then similar – pretty much the same document as it was used as a decoy was published publicly in the Ukraine, but not before. And the fact that we saw that actual scientific papers, but it was published after Primitive Bear used it, so that way we know that they actually have some way of stealing a real Ukrainian documents and using them, weaponizing them to use them in their attacks, rather than – another option would be just to create some fake document based on known facts. But it seems they use some stream of stolen documents for their purposes.
Dave Bittner: Yeah, that's an interesting lure there. I mean, you can imagine if someone was interested in the content of this sort of scientific document and they were able to get it ahead of other people, you know, sort of hot off the presses, if you were, if you will, that you could really imagine that working as clickbait.
Yury Polozov: Yes, absolutely. And we saw them using all kinds of topics for their lures, some legal questions, some questions around occupied Crimea. And Crimea is a diverse region, so they would use different languages, they would use Ukrainian, but sometimes they use Russian as well, because many people in eastern Ukraine and Crimea, they speak Russian. So all kinds of lures that they use and experiment with.
Dave Bittner: But some of the documents, I mean, themselves, they are legitimate documents, so they're stealing them or borrowing them from other sources, and using the legitimacy of those documents to try to get people to click through.
Yury Polozov: Yes, absolutely. And it makes it harder to detect with the human eye because it actually – they are documents that were used.
Dave Bittner: Right, right. So, in terms of people protecting themselves against this, what do you recommend? Is this something where endpoint protection would be able to notice that something was up?
Gage Mele: Yeah, I think potentially strange email addresses, so tools like that are always helpful, but a lot of it is just education on something seems too good to be true, for instance, early access to something, you know, maybe it is. And if you get an email from someone, maybe you should email that again and confirm that it was sent to you. A lot of sophisticated groups, unsophisticated groups, groups of all kinds, use a lot of social engineering as that initial infection chain, because it works, unfortunately.
Dave Bittner: Right. In terms of a Primitive Bear themselves, I mean, I suppose there's no reason to believe that they'll do anything other than keep at this, what they're doing. I mean, it seems like they've had some success, and I suppose we should expect to see more from them in the future.
Gage Mele: Yes, they've been busy. And I'm sure they use – you've seen research from other researchers out there, which is really good stuff as well, and different TTPs. It just so happens that this campaign was dedicated to these .docx files. But other TTPs are very likely in Primitive Bear's – or are in Primitive Bear's repertoire.
Yury Polozov: And of course, after this research, we really just saw new examples of the activity, but generally, Russian cyber activity is often part of larger geopolitical or military activity. So earlier this year, when fighting in eastern Ukraine was intensifying and Russia was moving troops closer to Ukrainian border, that's why we saw this campaign being more active, and it was an interesting timing. And also it was important that the international community just saw Russia moving its troops, but also saw Russia sending malicious emails towards Ukraine. And it prompted a stronger than usual response. And now most of those troops moved back, at least for now. And it's not the end of the story. Putin will continue trying to expand his empire, so to say. It's very weird.
Dave Bittner: Our thanks to Gage Mele and Yury Polozov from Anomali's threat research team. The research is titled, "Primitive Bear (Gamaredon) Targets Ukraine with Timely Themes." We'll have a link in the show notes.
Dave Bittner: The CyberWire Research Saturday is proudly produced in Maryland out of the startup studios of DataTribe, where they're co-building the next generation of cybersecurity teams and technologies. Our amazing CyberWire team is Elliott Peltzman, Puru Prakash, Kelsea Bond, Tim Nodar, Joe Carrigan, Carole Theriault, Ben Yelin, Nick Veliky, Gina Johnson, Bennett Moe, Chris Russell, John Petrik, Jennifer Eiben, Rick Howard, Peter Kilpe, and I'm Dave Bittner. Thanks for listening.


