You can add new features, just secure the old stuff first.
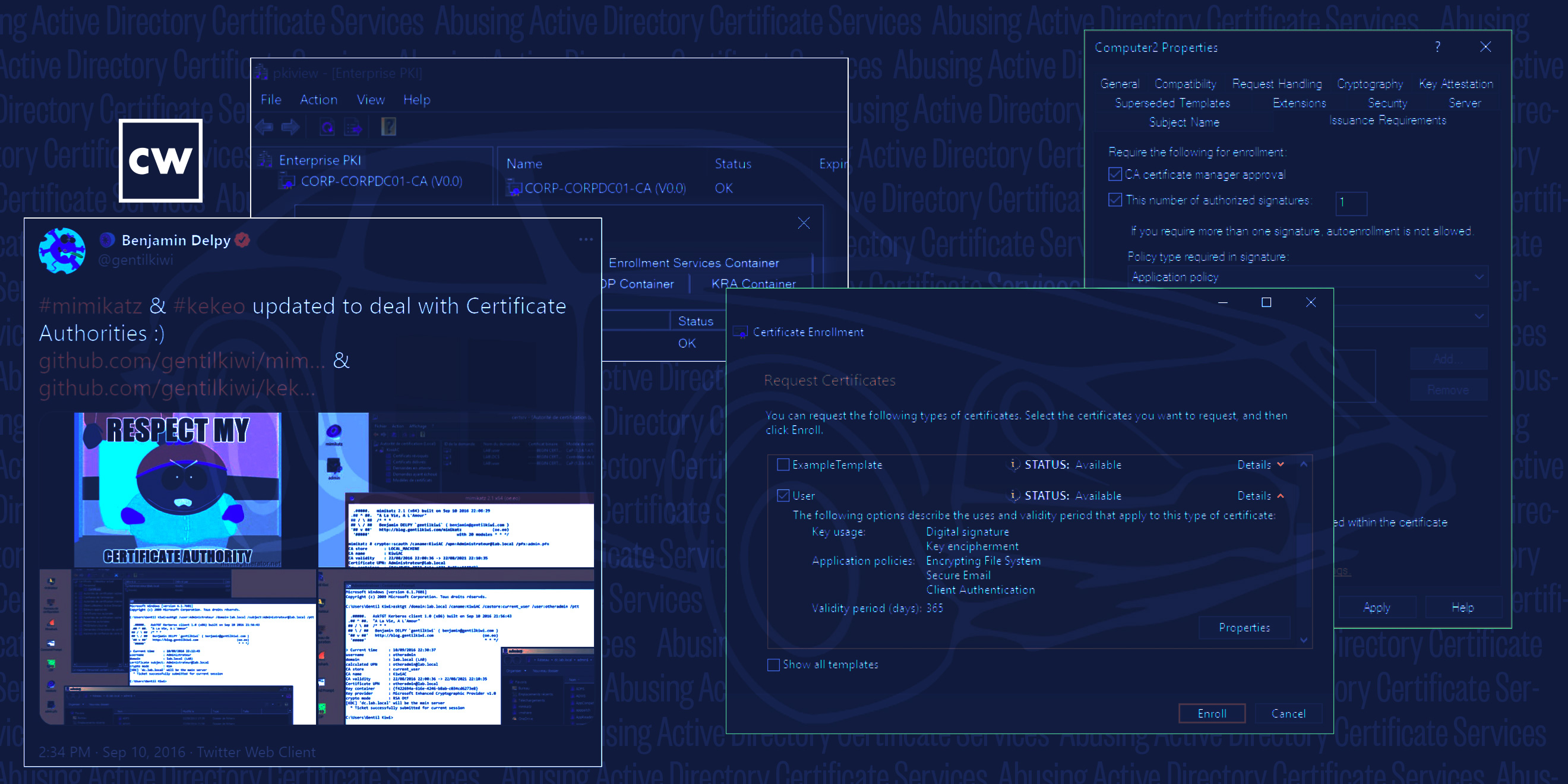
Guests Will Schroeder and Lee Christensen from SpecterOps join Dave to share the research they recently presented at Black Hat USA on the security of Microsoft's Active Directory Certificate Services.
Their abstract:
Microsoft’s Active Directory Public Key Infrastructure (PKI) implementation, known as Active Directory Certificate Services (AD CS), has largely flown under the radar of both the offensive and defensive communities. AD CS is widely deployed, and provides attackers opportunities for credential theft, machine persistence, domain escalation, and subtle domain persistence. We present relevant background on certificates in Active Directory, detail the abuse of AD CS through certificate theft and active malicious enrollments for user and machine persistence, discuss a set of common misconfigurations that can result in domain escalation, and explain a method for stealing a Certificate Authority’s private key in order to forge new user/machine “golden” certificates. By bringing light to the security implications of AD CS, we hope to raise awareness for both attackers and defenders alike of the security issues surrounding this complex, widely deployed, and often misunderstood system.
The blog post and white paper can be found here:
Note: Microsoft is a sponsor of the CyberWire, however, we cover them as we would any other company.



