SysJoker backdoor masquerades as benign updates.
Dave Bittner: Hello everyone, and welcome to the CyberWire's Research Saturday. I'm Dave Bittner, and this is our weekly conversation with researchers and analysts tracking down threats and vulnerabilities, solving some of the hard problems of protecting ourselves in a rapidly evolving cyberspace. Thanks for joining us.
Avigayil Mechtinger: So basically, SysJoker was found during an active attack on a Linux-based web server and after some research, we found out that SysJoker is actually has Mac and Windows versions.
Dave Bittner: Joining us today are Avigayil Mechtinger and Ryan Robinson, both security researchers at Intezer. The research is titled, "New SysJoker Backdoor Targets Windows, Linux, and macOS."
Dave Bittner: All right, well, let's walk through this together. Can we go through your technical analysis here? What exactly is going on with SysJoker?
Avigayil Mechtinger: Yeah. So I'll mention a few points before I dive into the technical analysis.
Dave Bittner: That's Avigayil Mechtinger.
Avigayil Mechtinger: So basically, SysJoker masquerades as a system update, and it has persistent capabilities. This means that it can survive reboot on the machine. And based on SysJoker's capability, we assessed that the goal of the attack is espionage. And also, it has lateral movement capabilities, which might also lead to a ransomware attack as one of the next stages.
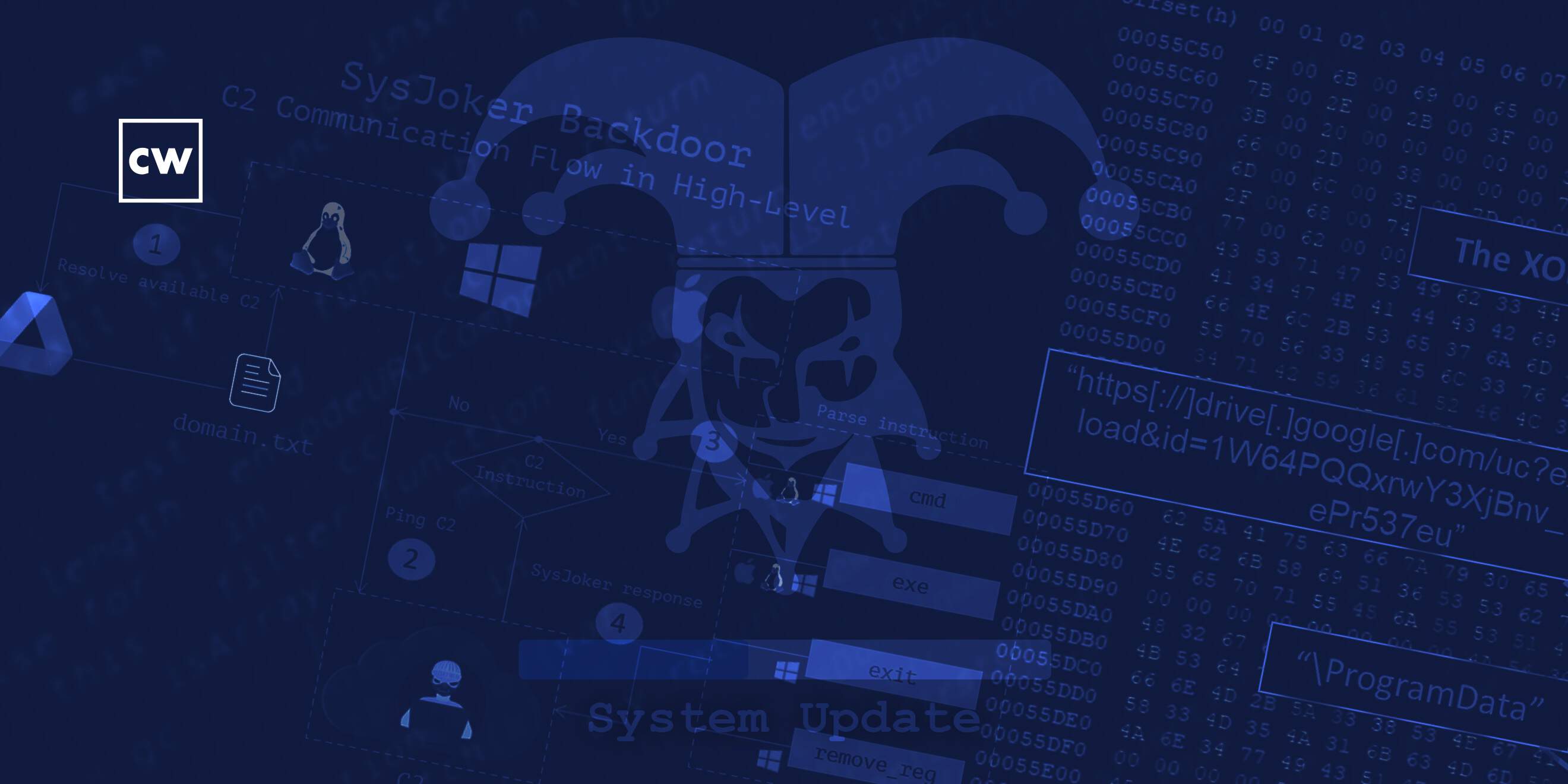
Avigayil Mechtinger: Now, if we go a bit more technically and high level, so, first, it will copy itself to a new directory masquerading as something benign on the machine. After that, it will start collecting information off the compromised machine, using living-off-the-land commands – for Windows, it's PowerShell. And then it will send the information of the machine to the command-and-control server as a first handshake. And then it will ping to the command-and-control server and wait for an instruction. And if there is an instruction, it will parse it and send the response back to the C2.
Avigayil Mechtinger: Now, SysJoker has full backdoor capabilities. It can receive two different instructions from the C2, basically. The first one is "cmd," which means run a command provided by the attacker and send the response back to the C2. And the second command is "exit," which means drop an executable from a provided URL and run it. This is really in the high level.
Avigayil Mechtinger: Now, SysJoker has an interesting way to resolve its C2, its command-and-control. It will first contact a hardcoded Google Drive URL, which hosts a "domain.txt" file, and this file contains a base64 decoded address. It will then decode this address with a hardcoded. XOR key, and this key is also used for decoding and encoding strings from within the binary itself, and also that is sent and received from the C2. Yeah, Ryan, would you like to continue with some more interesting points about this malware?
Ryan Robinson: So it'll mainly just be reiterating what you've said mostly...
Dave Bittner: Ryan Robinson.
Ryan Robinson: ...Yea, when it's first executed on the machine, it will copy itself to a location where it masquerades as something quite benign. So those are just like a system update or like a script file. In the Windows version, there is – since, when malware is quite often better detected through security tooling, it appears to have a first stage that uses PowerShell to sort of drop and execute the SysJoker payload. So it does that, but that doesn't exist on the Mac and the Linux versions.
Ryan Robinson: What is interesting about the Linux version is that they have sort of made an operational security gaffe, is that they have not stripped the binary so artifacts of what they actually called the the function – they're still in there. And also interesting as well, they have a logging system in place. So, what the malware does, it will write this down into, like, a log, and it kind of assists with analysis a lot, really.
Ryan Robinson: So, it does the logging sort of the same in the Mac version, but the functions have been stripped in that. What is also interesting with the Mac version is that it's compiled for a multi-arch. Therefore, we can probably assume that they want that to run on both the Intel versions of Mac and newer Mac machines that have the Apple M1 chip. It has an Arm version packed with a multi.
Dave Bittner: So, do you have any insights on how someone would find themselves infected with this? In other words, do we have a sense for who they're targeting and some of the specific ways that they'll get this onto their target systems?
Ryan Robinson: So, in regards to who they're targeting, definitely they have an interest in academic and science institutions. We can see this obviously through the compromised victim that we know of personally and that we've worked with. But also you can see in the domains that they have created. So one of the domains that they've created is called the "bookitlab," and this is a piece of software that's used by academic institutions, universities, colleges, and all for, like, facilities management. If you were to see this in your network, it looks like normal academic traffic, per se. So it seems to be quite an interest within that field. And also links that have sort of been on Twitter. Some other people have given attributions. There appears to be related to free passive DNS pivoting. It appears that there is a related side that is a weaponized Microsoft Office Word file that deals with science as well, that may be used as a first stage to deliver the malware. Also though our personal experience, we know that this malware is dropped in another instance through a reverse shell that was spawned through an exploited Apache Web server.
Dave Bittner: What is your advice in terms of folks detecting this and protecting themselves against infection to begin with?
Avigayil Mechtinger: To begin with, there are many security practices. First of all, checking that you're running the most updated systems and best practices of the configurations. It really differs whether you have a server or an endpoint and so on. There are many security practices, so if we're talking about the servers, then what I mentioned – there's this configuration and being updated to the latest services. And if we're talking of an endpoint, you can do phishing courses for the employees and so on. Complex passwords and, you know, the list goes on.
Avigayil Mechtinger: But as for detecting if you have been compromised, I can look you back to the blog that we wrote, where we provided detection content which can really help you searching via your EDR or SIEM really easily. And we also published another blog that explains how the OS queries, so there is information for that as well.
Dave Bittner: So how widespread is this? And are you seeing that this actor is still active out there, making this an ongoing campaign?
Avigayil Mechtinger: So, we have not observed many samples in the wild, and this suggests that the attacks are limited in scope. Actually, the C2 was up and running when we analyzed the files, and it actually changed three times during our analysis, which indicated that during our analysis, the attacker was, you know, was monitoring, was there, was updating its C2. But after the publication, the Google Drive links went down. And I think this kind of shut down some of the samples that we found. It could be that there will be new samples with new Google Drive links that will generate new C2s. It kind of provides them a way to go under the radar when they use this domain of Google. But for the samples that we found now, they don't have the ability to resolve the C2.
Dave Bittner: Our thanks to Avigayil Mechtinger and Ryan Robinson from Intezer for joining us. The research is titled, "New SysJoker Backdoor Targets Windows, Linux, and macOS." We'll have a link in the show notes.
Dave Bittner: The CyberWire Research Saturday is proudly produced in Maryland out of the startup studios of DataTribe, where they're co-building the next generation of cybersecurity teams and technologies. Our amazing CyberWire team is Elliott Peltzman, Tre Hester, Brandon Karpf, Eliana White, Puru Prakash, Justin Sabie, Tim Nodar, Joe Carrigan, Carole Theriault, Ben Yelin, Nick Veliky, Gina Johnson, Bennett Moe, Chris Russell, John Petrik, Jennifer Eiben, Rick Howard, Peter Kilpe, and I'm Dave Bittner. Thanks for listening. We'll see you back here next week.


