Instagram hijacks all start with a phish.
Dave Bittner: Hello everyone, and welcome to the CyberWire's Research Saturday. I'm Dave Bittner, and this is our weekly conversation with researchers and analysts tracking down threats and vulnerabilities, solving some of the hard problems of protecting ourselves in a rapidly evolving cyberspace. Thanks for joining us.
Marcelle Lee: So, it was kind of funny, it actually came through one of our VPs. They had a friend that this had happened to with their corporate Instagram account. So this person reached out and was like, do you want to know about this? And then it got kicked down the chain and I picked it up because it seemed kind of interesting.
Dave Bittner: That's Marcelle Lee. She's a Senior Security Researcher and Emerging Threats Lead at Secureworks. The research we're discussing today is titled, "Ransoms Demanded for Hijacked Instagram Accounts."
Dave Bittner: Let's walk through it together here. Can you sort of take us through how someone would find themselves a victim of this particular attack?
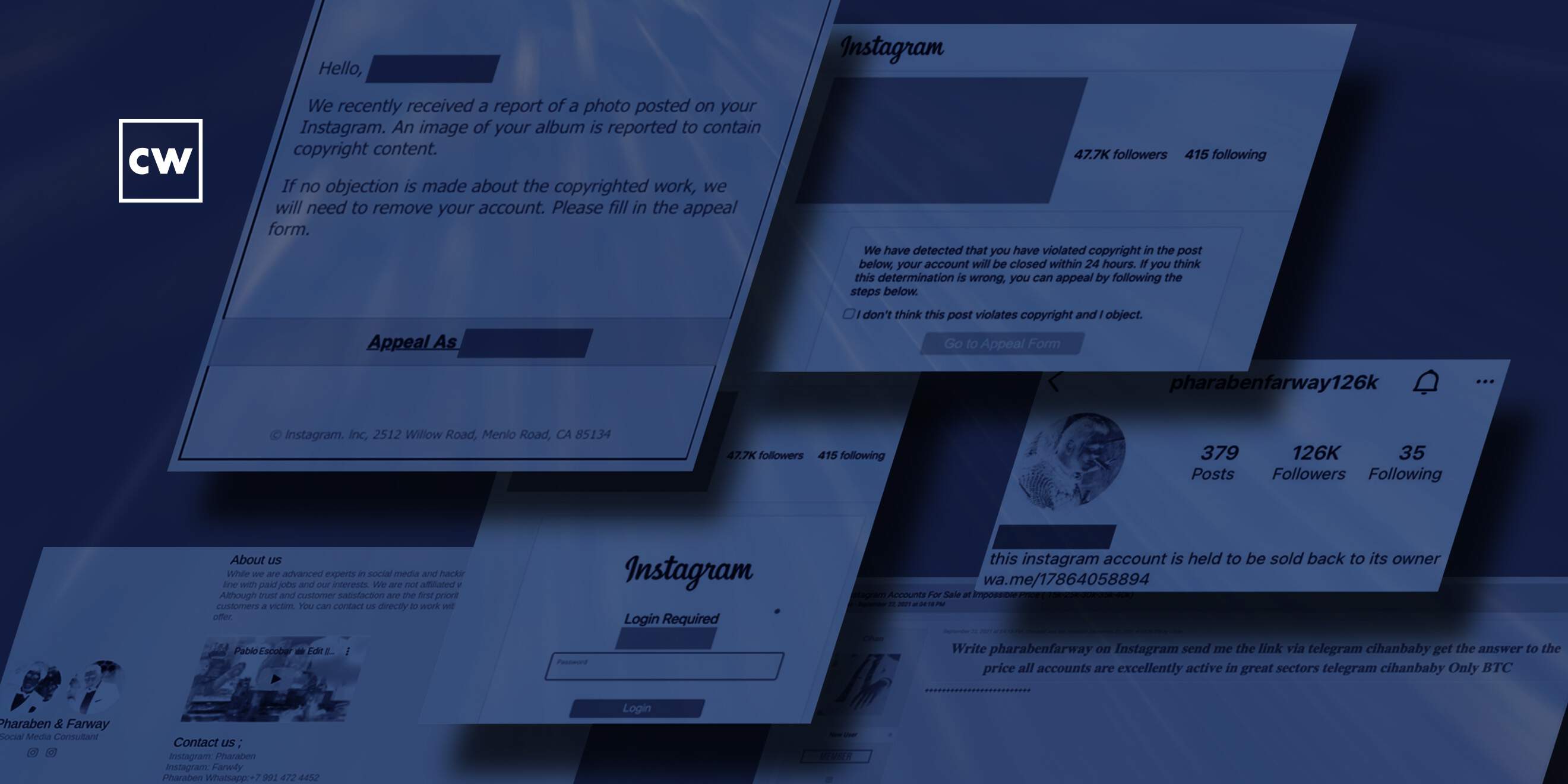
Marcelle Lee: Yeah, absolutely. So, it all starts with a phish, unsurprisingly, right? As many things do, starting with a phish. And the threat actors had an interesting campaign that they were running, where they would send a message either via Instagram or via email to their target. And it said, essentially, that there had been some kind of, you know, copyright infringement for something that they had posted on Instagram, and please click on this link to, you know, appeal it, basically. So I thought it was unique in, like, I've not seen that particular kind of lure used before. I mean, obviously there's tons of phishing out there, but I don't know that I've seen copyright infringement before.
Dave Bittner: Yeah, it's interesting in that it struck me as being simultaneously benign, but also urgent, because it's not – I mean, a copyright violation, you know, OK, you could see that happening in the course of day-to-day stuff, certainly on Instagram. But then the message says, if you don't follow through on this, we'll need to remove your account.
Marcelle Lee: Yes, yes, exactly. So, of course, it does have a bit of that sense of urgency, depending on how much you care about your Instagram account, I guess.
Dave Bittner: Right.
Marcelle Lee: And you know as well as I do that all this phishing works on different psychological principles. So I think really urgency and perhaps authority would be the two that I would think of for this particular phish. So, and it was also customized, you know, very specifically for their target. So, you know, it had the person's name and their Instagram handle, so it wasn't just something that was just cast out there kind of widely and not targeted at all. It was very specific. And, you know, as we revealed eventually in the research is that, you know, they were specifically going after corporate accounts or accounts that had a high number of followers, presumably because those accounts would be more inclined to cough up a ransom to get their access back.
Dave Bittner: So, if I click through on here and I think my Instagram account is in peril, what would happen next?
Marcelle Lee: So the next thing that happens is a page comes up, and it's a pretty good copy of Instagram's actual page. And again, another warning message telling you to go to the appeal form, but you have to log in at this point. And of course, you're not on the actual Instagram site. You're on a fake Instagram site, but a very well-done fake Instagram site. You know, there's a whole tier of how good these things look, and these were pretty slick, and I actually visited a number of them myself to see what it looked like. And the domain names that the threat actors were using, you know, the for the fake Instagram pages had things around like "support" and "support violation form," a lot of IG hyphen this, that, or the other. So it kind of had the appearance of maybe being legitimate for anybody who was actually looking at the link closely. They did set up quite a number of different domains. And I mean, as of last week, this is still ongoing, so I haven't looked lately, but I'm sure there's probably even more domains than what we listed in the blog post.
Dave Bittner: So it then takes you to a fake login screen, and from there, what happens?
Marcelle Lee: So essentially, you'll put it in your password – not you, of course, but you're way too savvy for that...
Dave Bittner: (Laughs)
Marcelle Lee: ...But the victim would put in their password, and at that point, behind the scenes on this fake website, they harvest that information and then, you know, presto manifesto, they now have the credentials for your Instagram account. And so they immediately take over the account and then modify the account page – like, the Instagram social media page – to show that it's been, you know, taken over by these threat actors.
Dave Bittner: Yeah, that was a fascinating element of this to me, is you all have a screen capture here in the research, and they modify, I guess, the About page on the account, and it says this Instagram account is held to be sold back to its owner.
Marcelle Lee: Yeah.
Dave Bittner: And then they have their own, I guess, their own name in there as well. Can you unpack that for us?
Marcelle Lee: Yeah, sure. So the "pharabenfarway" seems to be a combination of the two threat actors' names behind this whole campaign. Then they tack on, after pharabenfarway, a number. And so, like in the example in the blog post, it's "126k," which – actually I didn't notice this, somebody else in my team noticed this – it's like, oh, that aligns with the number of followers. So that seems to be the methodology for the naming of the account, and it has the WhatsApp phone number, basically – or contact, not a phone number per se – but a WhatsApp domain with a contact number there for them to reach back to. It's interesting because I didn't used to be a big Instagram user and I ended up getting an account just because I'm often doing research that involves Instagram and you can't really see that much unless you have an account. So now, like I just checked the other day, and if you search for pharabenfarway, you know, just in the search function of Instagram, you'll see there's many, many, many instances of these hijacked accounts, and some of them, you could tell what they are just by looking at the posts from the Instagram account, other ones you can't really. And I've also seen sort of, anecdotally, a number of people posting, you know, oh, my Instagram account has been taken over by these people, what do I do? So, yeah, they're pretty prolific. I was really surprised at the extent of the activity.
Dave Bittner: I have to say that that part of it leaves me scratching my head a bit, that if they're so out there in the open and they're consistently using this name, this calling card, how has that not drawn the attention of Instagram to instantly and automatically shut this sort of thing down when they see it? That puzzles me.
Marcelle Lee: Yeah, it puzzles me too. I couldn't really opine on why or how Instagram does these things, but I think they're usually pretty on, you know, campaigns like this, and I would imagine there would be a number of people who would have contacted Instagram about it. So, you know, these guys – I'll call them guys, they may be women, but all their avatars and everything look like men – their opsec is not super strong, right? It wasn't hard to find their email addresses and their phone numbers and so on and so forth. So maybe now that this blog is out, Instagram will take them down.
Dave Bittner: Well, let's hope. Well, you mentioned them having poor OPSEC. Let's explore that part together. How did you go down that pathway and what were you able to discover?
Marcelle Lee: Yeah. So I was able to discover some other contact information through, actually, some of the domain registrations were not private, which is rare these days – almost always when you're going down that particular rabbit hole, it's mostly a dead end. But in this case, it wasn't. And then they actually had their own little website with an "About us" page that kind of said a little bit about who they were and apparently they're into, I don't know, I think it's Robert – no, I don't even know who these actors are. I think it's the guy from Scarface. And then I'm not sure the other one is. You might know.
Dave Bittner: Yeah, just it looks like maybe Pablo Escobar and Al Pacino maybe.
Marcelle Lee: There you go.
Dave Bittner: A couple of gangsters. Imagine that – two threat actors using images of gangsters in their iconography.
Marcelle Lee: (Laughs) Right, exactly. So they have their, you know, their individual Instagram accounts and their WhatsApp phone numbers. So, and again, they're using the same name or sort of, you know, permutations of that pharabenfarway thing. So that was actually not too hard to discover. And then they also had the underground forum listing where they were saying that they would offer access to these accounts for sale, potentially. So they left a lot of breadcrumbs, I would say, basically.
Dave Bittner: And so, part of this is that they're trying to ransom these accounts back to their original owners. As you pointed out, they seem to be targeting corporate accounts, where I suppose they feel as though they might be more inclined to open up their wallet.
Marcelle Lee: Mm-hmm. And I mean, honestly – and I don't think I got into this in the blog – but they weren't asking exorbitant ransom amounts, at least not that I saw. The few where I was able to see the amount being asked, it was, you know, around like five-hundred dollars. So I think, you know, they're in it for volume. And you know, if you you can get a hundred different companies to pay you five-hundred dollars in a week or whatever, then that's not too bad.
Dave Bittner: Yeah, yeah, almost a nuisance, and I suppose I don't want to go so far as to say an investment in reminding a company that they should be using multifactor authentication. But there you go. (Laughs)
Marcelle Lee: I think I would pay you five-hundred dollars to get that kind of advice if I was an organization. (Laughs)
Dave Bittner: Yeah, yeah. What were you able to suss out here in terms of where these folks might be coming from?
Marcelle Lee: Yes, so there were some breadcrumbs here as well. You know, we tend to kind of assume that all the cybercrime type stuff is coming out of Russia, but not necessarily. And in this case, it seemed like one of the threat actors was from Russia, but the other one appeared to be from Turkey, which is not something that I see all that commonly. And you know, some of the things that pointed towards that were, in this case, he had a Russian country code for his phone number. And then in the page source basically of these different phishing sites, there is a document sharing service that they were using to reference different files. And that document sharing service was a Turkish company, hizliresim[.]com – I'm sure I'm mutilating the pronunciation of that. But, you know, I was like, oh, that's interesting. And then there were a couple of instances where I found the Instagram account being used to communicate with the victims was a Turkish-language version of Instagram. So yeah, so it pointed certainly to at least one of these threat actors being based in Turkey.
Dave Bittner: Yeah. So what are your recommendations, then? If I'm the person at my organization who's charged with, you know, protecting our WhatsApp social media account, what sort of things can I put in place to keep these folks away?
Marcelle Lee: Yeah. Well, you already said the number one thing, right? Multifactor authentication. It doesn't cure everything, but it certainly presents a stumbling block. So, you know, if you're trying to hack into somebody's whatever account, right, if there's multi-factor authentication, it's just going to make it that much harder. And chances are you're just going to move on to the next potential victim. And we see that all the time at Secureworks with, you know, not Instagram hacking, but just really, you know, trying to get in through like VPN access or or whatever. You know, multifactor authentication is almost always one of our top recommendations around, like, incident response engagements that we do.
Marcelle Lee: I think with social media sometimes too, like, I think shared logins are used. Like, you know, a company might have like, you know, social media at XYZ Company or Instagram at XYZ Company, which is, A, easy to guess, and B, the password being shared around. So that's not a super great practice. It's much better to have something unique that, you know, only one person has access to, or of course, use a password manager where it's, you know, that's something I always recommend to people anyway. Then you don't have to be sending passwords around by text or email or carrier pigeon, whatever people.
Dave Bittner: The other thing that strikes me about password managers that I don't hear people mention all that often is that a lot of them will try to protect you from logging in to a spoofed site. You know, like, it'll check the URL and come back to you and say, hey, are you sure about this? Because we don't really think this is Instagram.
Marcelle Lee: Yeah. Are you sure you want to fill in? That's the one that I use all the time, and it's usually because I'm on like some mobile version or something that it's not recognizing. But yeah, absolutely. That's a great point, because it's another sort of safety measure that is baked into a lot of the password managers. And also, you know, the password managers will, of course, let you know if you're reusing passwords. And that's, you know, that's the thing that concerns me about this kind of campaign. It's like, sure, maybe you don't really care that much if your Instagram account gets hacked. But if you're using like the same credentials for, you know, corporate access your email or whatever, which as we know people do tend to reuse, then that's not great, you know, then it turns into a whole different level of being problematic. So, definitely password managers help with that aspect, too.
Dave Bittner: Do you have any sense for how successful this gang has been? Is there any Bitcoin accounts or anything like that, that we have any notion for how many folks are paying up?
Marcelle Lee: Yeah, I did come across wallet IDs and it looked like basically, at the time that I originally did the research which was a couple of months ago, they had been making many transactions, like, in and out, but it looked like they were pretty consistently having a balance of like twenty-thousand at a time before they would move it out to someplace else or something. So again, you know, not a huge amount, you know, when we're used to hearing about ransoms that are, you know, in the millions and millions of dollars. But you know, they clearly have been successful in this campaign and continue to do it, as far as I know.
Dave Bittner: Our thanks to Marcelle Lee from Secureworks for joining us. The research is titled, "Ransoms Demanded for Hijacked Instagram Accounts." We'll have a link in the show notes.
Dave Bittner: The CyberWire Research Saturday is proudly produced in Maryland out of the startup studios of DataTribe, where they're co-building the next generation of cybersecurity teams and technologies. Our amazing CyberWire team is Elliott Peltzman, Tre Hester, Brandon Karpf, Eliana White, Puru Prakash, Justin Sabie, Tim Nodar, Joe Carrigan, Carole Theriault, Ben Yelin, Nick Veliky, Gina Johnson, Bennett Moe, Chris Russell, John Petrik, Jennifer Eiben, Rick Howard, Peter Kilpe, and I'm Dave Bittner. Thanks for listening. We'll see you back here next week.


