Targeting routers to hit gaming servers.
Researchers at Palo Alto Networks' Unit 42 recently published research outlining attacks on home and small-business routers, taking advantage of known vulnerabilities to make the routers parts of botnets, ultimately used to attack gaming servers. Jen Miller-Osborn is the Deputy Director of Threat Intelligence for Unit 42 at Palo Alto Networks. She joins us to share their findings.
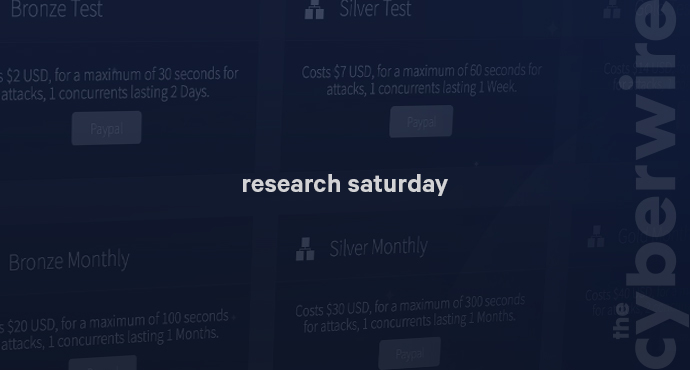
The research can be found here:



