Exhibiting advanced APT-like behavior.
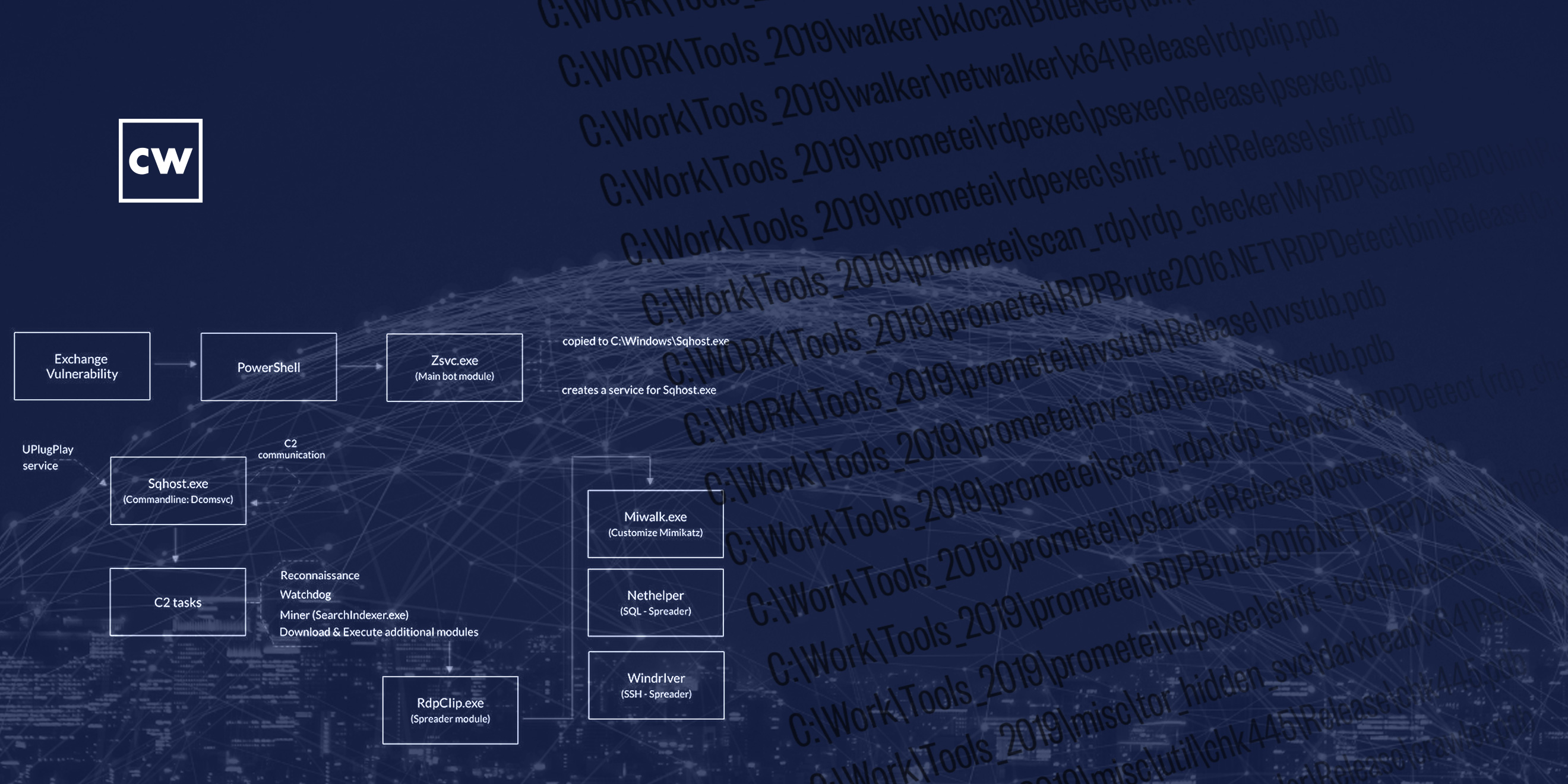
Guest Yonatan Striem-Amit joins Dave to talk about Cybereason's research "Prometei Botnet Exploiting Microsoft Exchange Vulnerabilities." The Cybereason Nocturnus Team responded to several incident response (IR) cases involving infections of the Prometei Botnet against companies in North America, observing that the attackers exploited recently published Microsoft Exchange vulnerabilities (CVE-2021-27065 and CVE-2021-26858) in order to penetrate the network and install malware. Yonatan shares his team's findings of the investigation of the attacks, including the initial foothold sequence of the attackers, the functionality of the different components of the malware, the threat actors’ origin and the bot’s infrastructure.
The research can be found here:



